
Wednesday, May 22, 2019
2:00 PM GMT / 9:00 AM EST
Security starts with the edge of your network. The connection and management of your chosen security devices requires careful thought and consideration of your network’s needs, with the resiliency and ease of management of these security devices being a critical aspect.

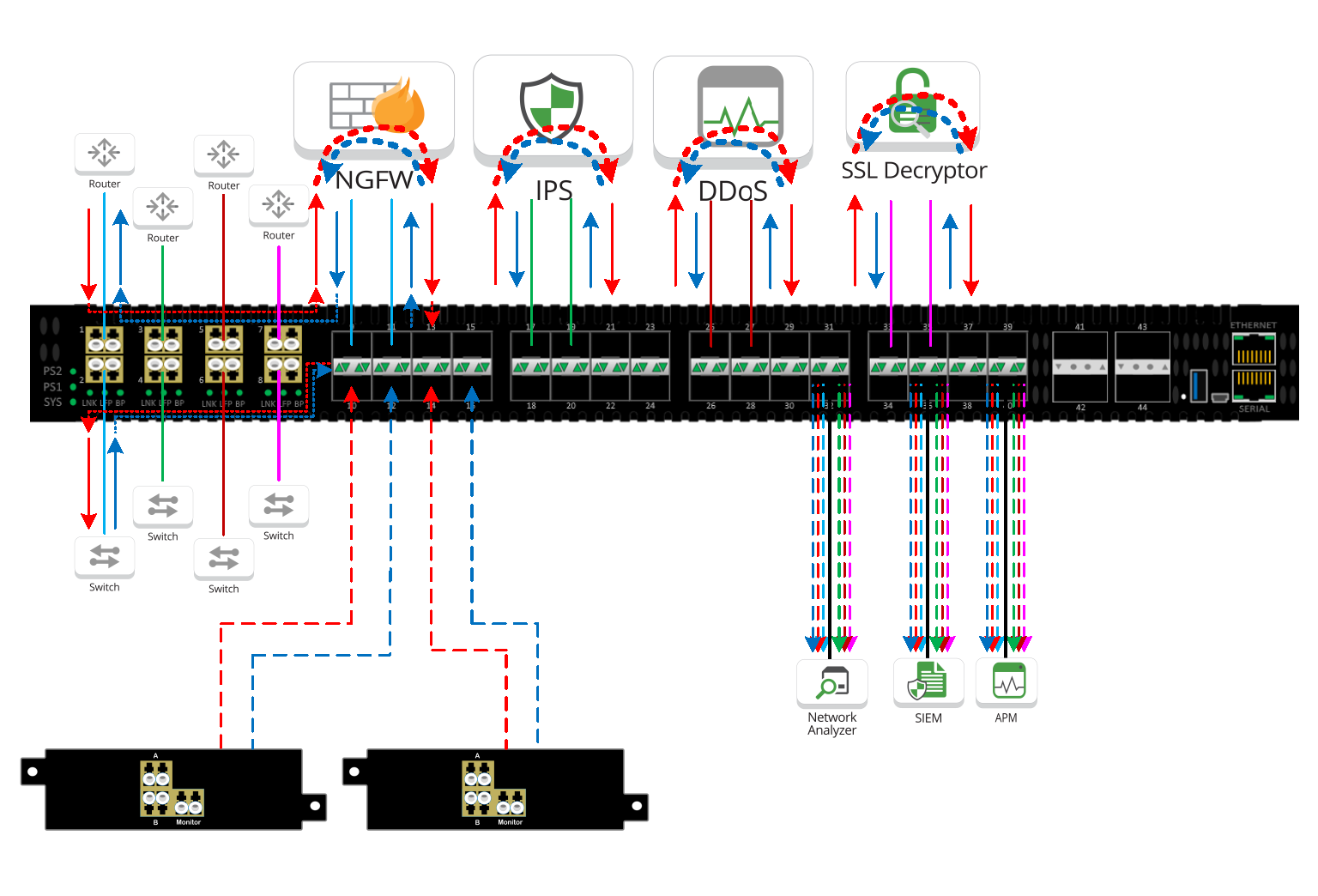
Best practices for connecting inline security devices
4 common inline security appliance connectivity scenarios
Challenges when deploying multiple inline security appliances at the edge of your network
The benefit of a chained Network Visibility approach