
December 14, 2017

We recently partnered with ExtraHop, a leader in real-time IT Analytics, which gives IT Operations, Network, and Security teams comprehensive visibility across everything from network performance to website user experience.
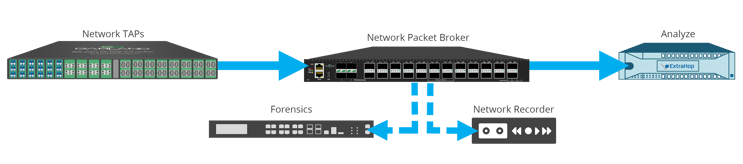
The Garland and ExtraHop platform partnership provides 100% network visibility with an end-to-end infrastructure that eliminates network blind spots. Garland’s network TAPs and packet brokers tap at the live wire for 100% packet capture. By securing the data at the physical layer through reliable network TAPs, the ExtraHop platform provides real-time application visibility to monitor, protect, block, and analyze traffic in real time, all the time.
[Learn more about what may be missing in your Network , with our free white paper, 7 Tools to TAP.]
Scalable network TAPs and packet brokers enable future network growth, from 1G/10G today to 25G/40G/100G tomorrow, with the most reliable data capture available. Purpose-built network packet brokers filter, aggregate, and load balance to one or many monitoring ports.
Upon receiving a copy of network traffic from Garland, the stream processor performs line-rate decryption, protocol decoding, and full-stream reassembly for every transaction, up to a sustained 40 Gbps. The result: Customers get deeper and more meaningful insight at a fraction of the cost compared to other real-time analytics solutions.
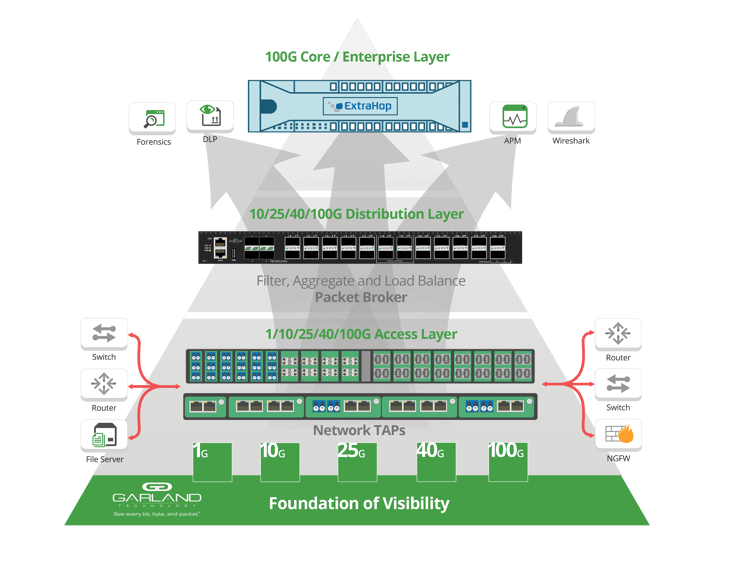
This solution delivers data-driven, real-time application (L2-L7) network monitoring and security solutions based on wire data, and guarantee no dropped or distorted packets as well as accurate relationships of frames, spacing, and response times with Garland’s passive fiber TAPs and network packet brokers.
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.