Resources
Insights for Network Visibility and Security
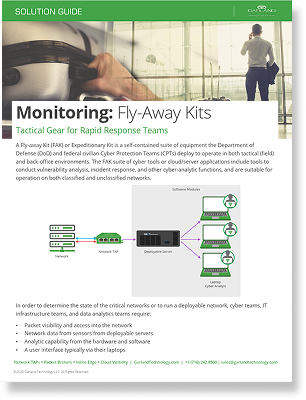
Blog
Webinar
Network Design Support
Looking to add network visibility, but not sure where to start?
Schedule a call with our experienced engineers for a free network design consultation. Our team of skilled network professionals shares your passion for solving complex challenges in network connectivity, visibility, access, monitoring, and security. Let us help you optimize your network with tailored solutions.