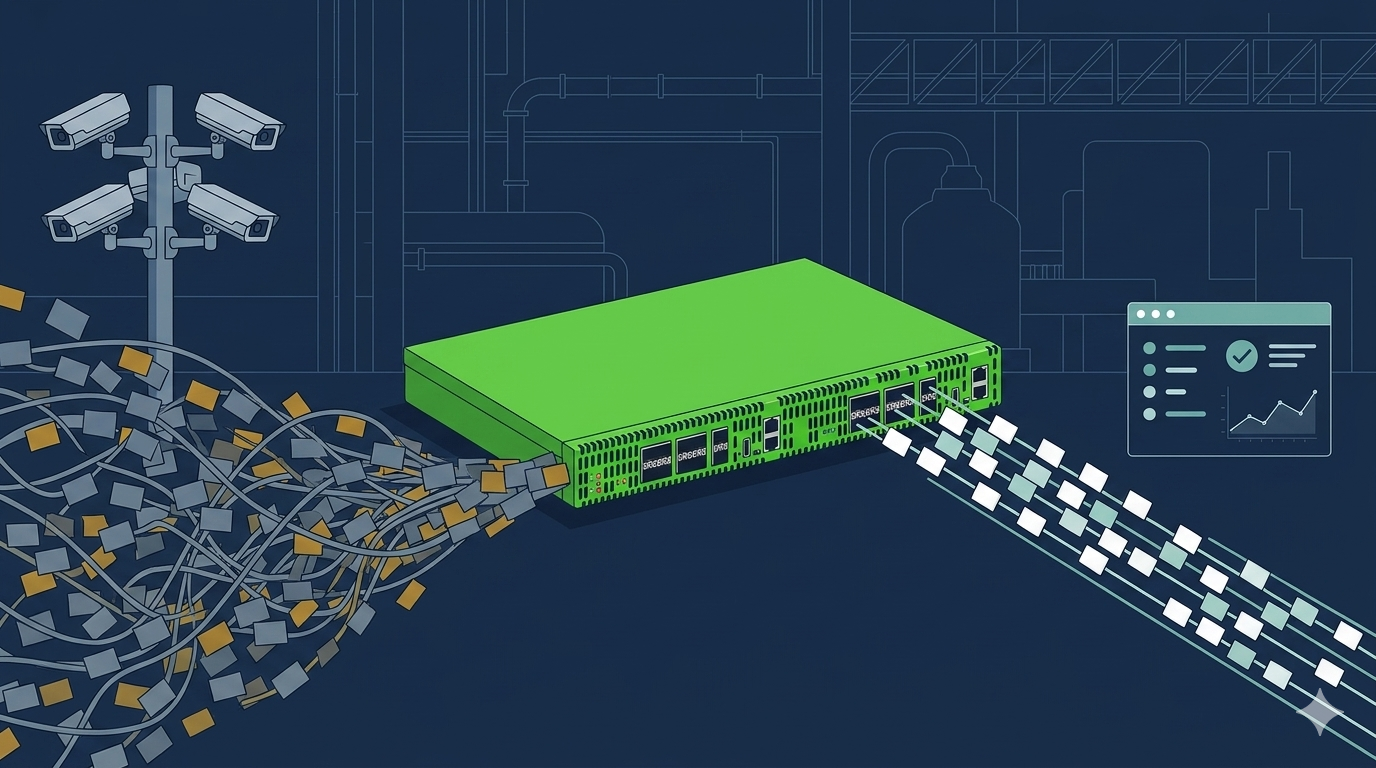
The 101 Series: Filtering TAPs
In our 101 network TAP series, we have explained the functionality of the various network TAPs that are available to gain access to the traffic that is typically found in a network. We have reviewed...