

Since virtually all attacks cross the network, security professionals need to make fast sense of what’s actually happening with their traffic. Easier said than done, however, given the challenges associated with:
Environments with high throughput traffic and limited data center space can find these challenges especially vexing and often settle for limited network visibility. They shouldn’t. An integrated solution from Garland Technology and Corelight can help organizations capture and analyze all of their network traffic at scale, reducing risk by dramatically accelerating both the speed and scope of security insights and operations.
Garland Technology’s compact, high performance network TAPs and Advanced Aggregators can reliably deliver a copy of network traffic to out-of-band Corelight Sensors, which transform the raw traffic into comprehensive network logs, extracted files, and custom security insights via the power of the Bro Network Security Monitor framework (aka “Bro”). The diagram below shows how the integration works:
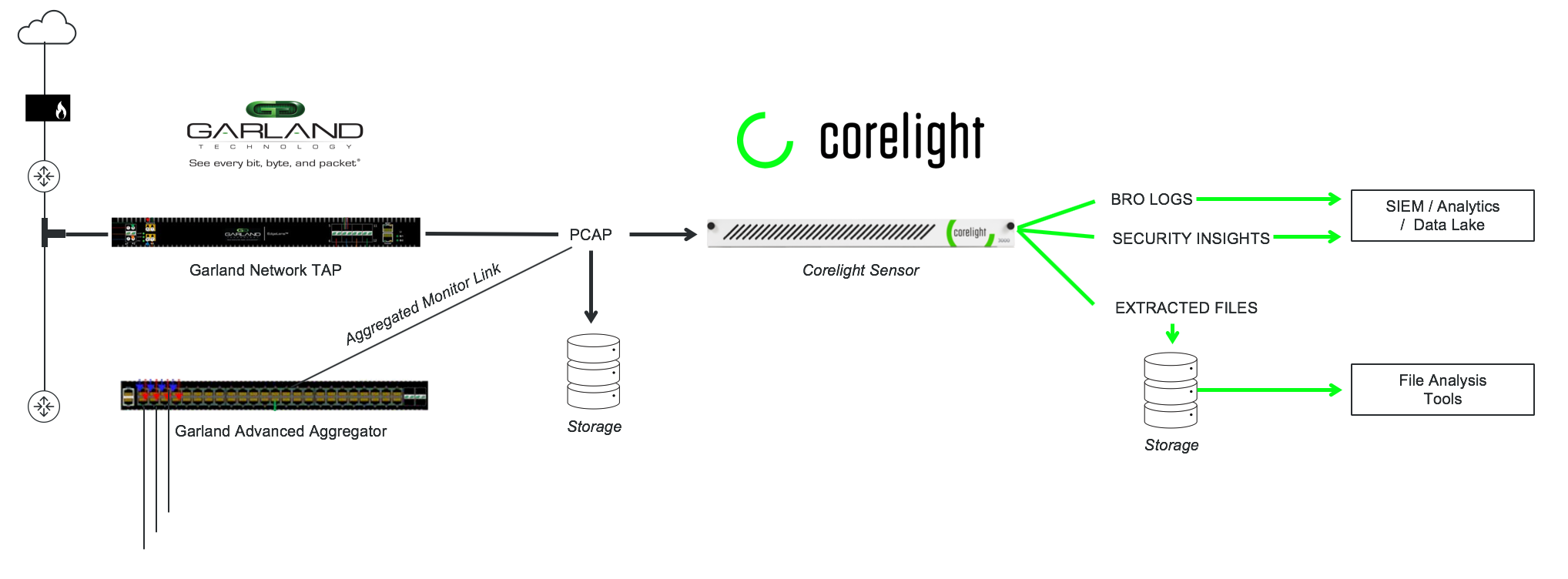
Corelight Sensors add enterprise level functionality and support to the network analysis framework of Bro. Since the sensors come pre-loaded with Bro packages, you can have actionable traffic insights right out of the box. It's as simple as tapping a network link with a Garland Technology TAP and feeding the traffic to the Corelight Sensor.
The Garland TAPs ensure 100% failsafe packet capture, while the Advanced Aggregator allows for full control over traffic behavior through filtering, aggregation and load balancing. The Corelight Sensors can then extract and log all network traffic, organized by protocol, which makes it easy for SOC/DFIR team to investigate and resolve any security incidents. .png?width=504&name=Corelight%20-%20AP3000%20(2).png)
High Speed Scalability
[Interested in learning more about the Garland Technology + Corelight Joint Solution? Watch our latest webinar]
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.