It’s a well known fact that financial institutions are the biggest target of data breaches, with that single sector comprising 35% of all data breaches worldwide. With billions of dollars at stake, companies are realizing that they must take every step necessary in order to secure their critical infrastructure from a breach. Taking these extra steps to protect their network is important in order to secure confidential customer data, and protect their reputation, and bottom line in case a breach does occur.
Thanks to recent GDPR regulations, companies that control or process personal identifiable data (such as names, addresses, phone numbers, dates of birth, etc.) on EU citizens, only have 72 hours after they learn about a breach to notify data subjects. Depending on the severity of breach, the number of affected data subjects, and the steps the company took to protect their subjects’ data, organizations can be fined up to €20 million or 4% of global annual turnover, whichever amount is higher.
With almost all financial institutions doing at least a portion of their operations online, it is very likely that they will have customers who are EU citizens, and thus fall under the previously mentioned GDPR regulations.
That’s why it’s extremely important for banks and investment firms to take extra measures towards securing their network. And that starts with implementing Garland’s EdgeSafe™ Bypass TAPs and EdgeLens® Inline Security Packet Brokers to manage their inline appliances.
Complete network visibility is needed in order to identify where malicious web application activity is occurring on the network. While a Web Application Firewall (WAF) is capable of filtering, monitoring, and blocking HTTP traffic being sent and received from a specific web application, configuration errors can also be an issue if the WAF is not blocking traffic correctly. So how do you overcome lack of visibility and find a way to troubleshoot your WAF?
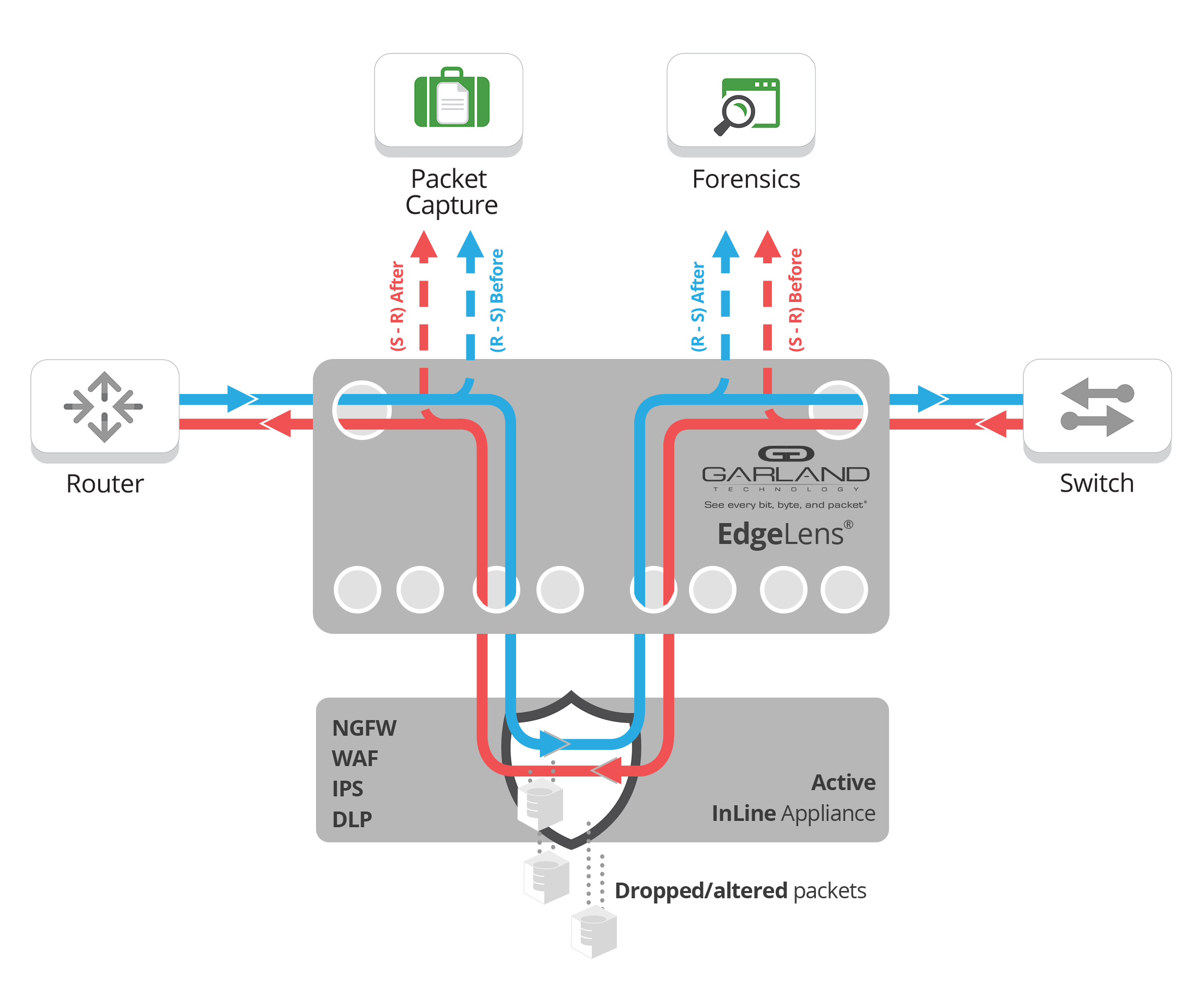
Garland’s EdgeLens® Inline Security Packet Broker transforms network security capabilities by capturing traffic both before it goes into the web application firewall, and after, sending both copies of data to performance monitoring tools, providing ultimate visibility coverage. This solution allows you to analyze your inline device to see if it is configured properly, or if it may be missing the threat.
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.