Why Cybersecurity Engineers Must Rethink Inline Security After the Latest Wave of Data Breaches
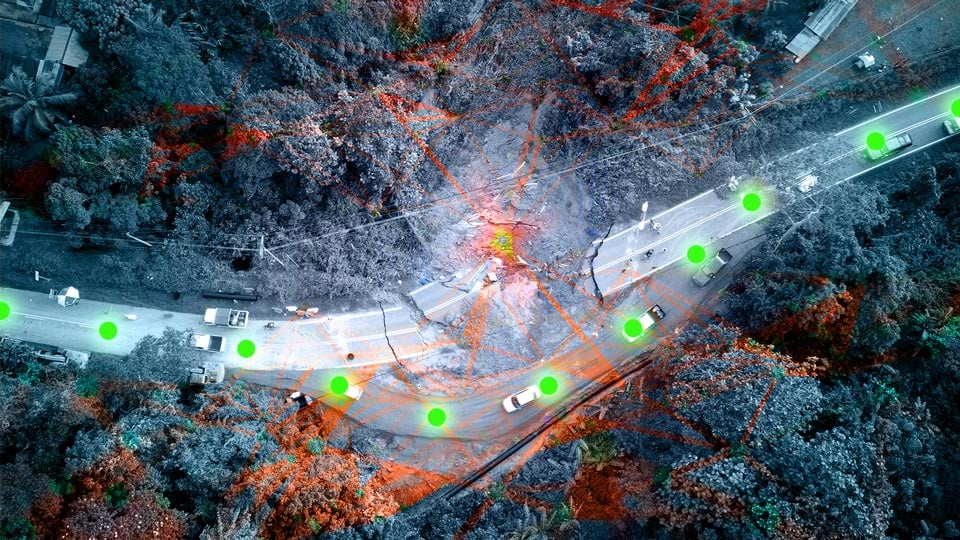
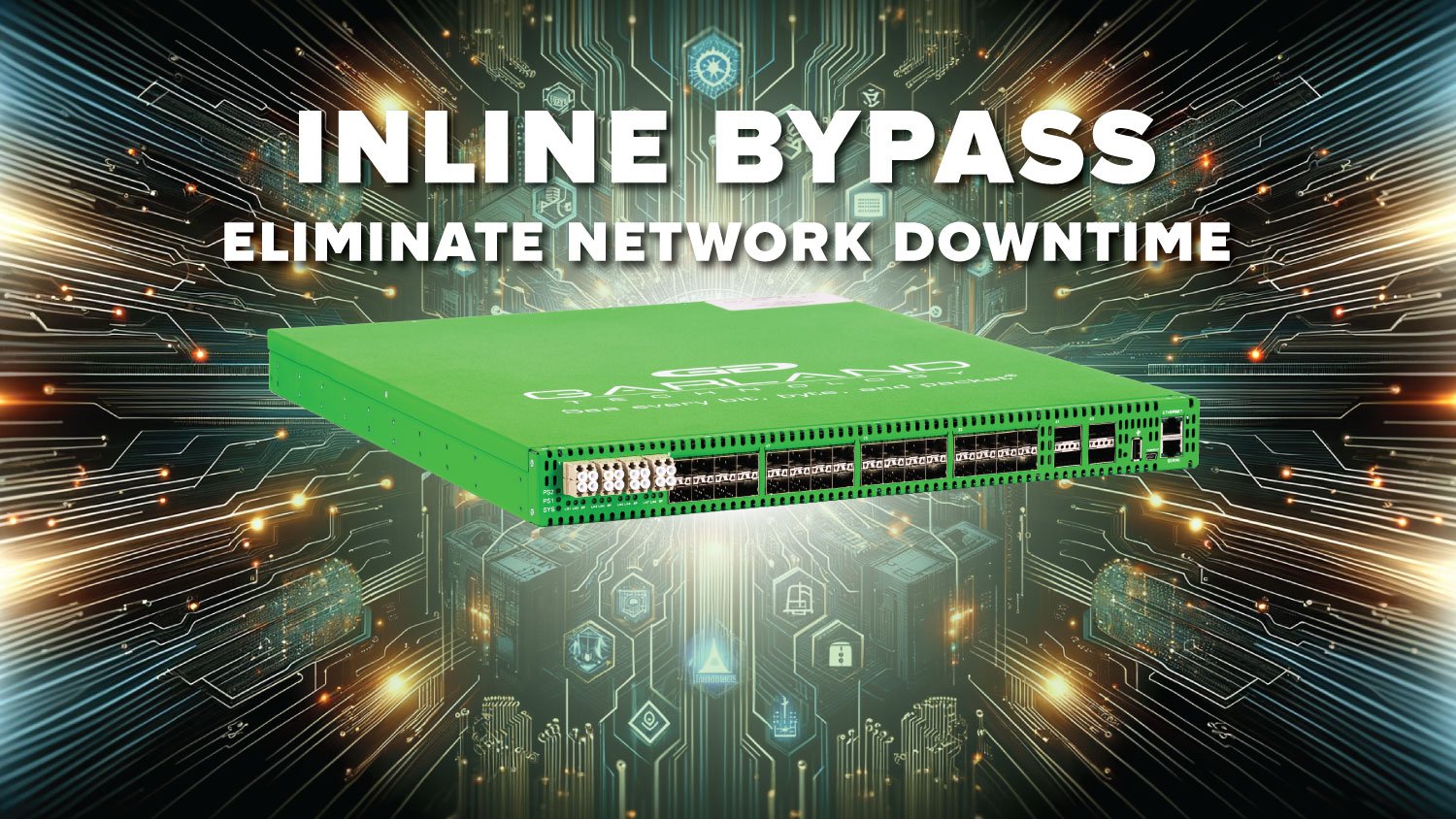
Recent global cyberattacks highlight weaknesses in traditional security architectures. Many organizations rely heavily on inline tools that can introduce operational risk and visibility gaps. Network...