

Cisco ACI is a game changing approach to managing networks across major disruptions including virtualization, multiple active data centers, hybrid data centers, and private and public cloud. Cisco ACI enables significant advantages in managing and deploying applications in these changing environments.
With these advantages comes additional planning in defending critical infrastructure across these extended data center architectures including physical, virtual and cloud. In particular, the deployment of inline tools like IPS and firewalls is critical in protecting these assets. These inline deployments are facilitated by using EdgeLens® Inline Security Packet Broker to manage these assets. In addition, EdgeLens can be used to gain additional visibility across the Cisco ACI fabric and deployment of other analysis tools.
Cisco ACI facilitates the Next Generation Data Center through multiple features that enable DC scalability, flexibility, and automation. Cisco ACI architecture advantages can also be extended to address security challenges. This is done by integrating security in the Application from day one. In addition, Cisco ACI can be used to accelerate security deployment and also automate security insertion through policy flows. 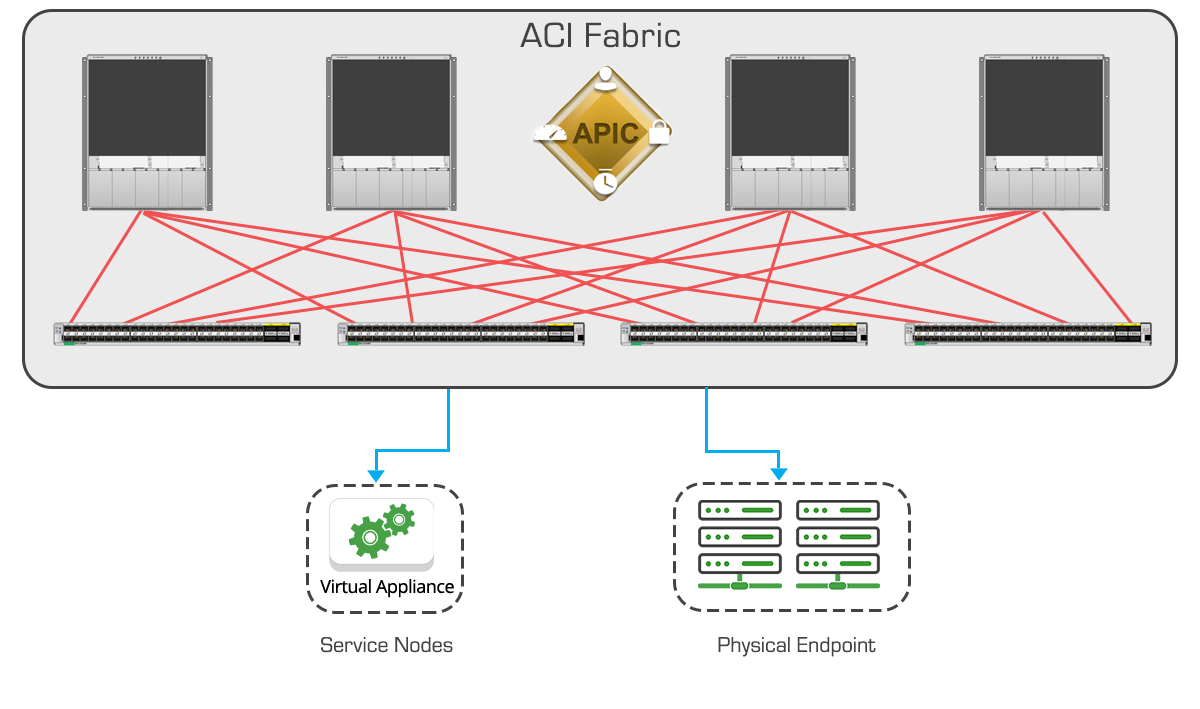
Security deployments and visibility are further aided by introducing EdgeLens security monitoring to manage inline security appliances, and aggregate wider level visibility to additional security tools like IDS and vulnerability management. This blog series will focus on key Cisco ACI definitions/concepts and highlight how to utilize EdgeLens to further secure your Cisco ACI deployment.
Cisco ACI is software defined networking environment. A classic definition involves networking architecture that is programmable and adaptable for the high-bandwidth and dynamic nature of the network’s latest software applications. SDN architecture decouples the network control and forwarding functions; enabling programmable network control and abstraction of applications from the underlying infrastructure.
A Cisco Application Centric Infrastructure (ACI) requires specific items including: Cisco Nexus 9000 series switch fabric with the Application Programming Interface Controller (APIC) to run in the leaf/spine ACI fabric. The Spine/Leaf network connects each leaf node to each spine node; with all other devices connected to leaf nodes. This includes the APIC which manages the ACI fabric. The APIC fabric management functions do not operate in the data path of the fabric.
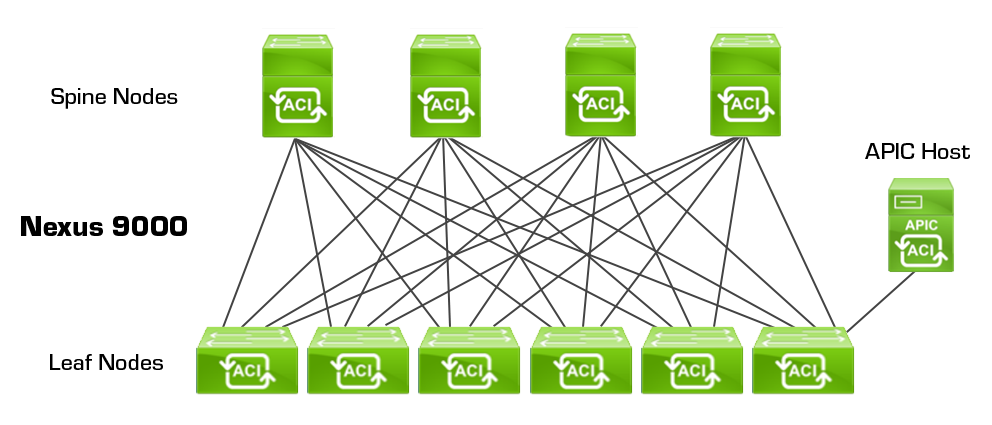
The ACI fabric provides forwarding across high-bandwidth links (40 Gbps and 100-Gbps). Traffic with the source and destination on the same leaf switch is handled locally, and all other traffic travels from the ingress leaf to the egress leaf through a spine switch. The fabric operates as a single Layer 3 switch. The ACI object-oriented operating system (OS) runs on each Cisco Nexus 9000 Series node. It enables programming of objects for each configurable element of the system. The ACI fabric OS renders policies from the APIC into a concrete model that runs in the physical infrastructure.
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.