Sometimes we come across interesting requests from customers that are outside the normal security and monitoring applications within data centers or branch office locations. Recently, a law enforcement agency reached out to Garland Technology with a question as to whether our Network TAPs could assist them in obtaining sound digital evidence for a trial. This is a great example of lawful intercept, a scenario when a government law enforcement agency is granted legal means to obtain communications network data pursuant to lawful authority for the purpose of analysis or evidence. It’s a similar concept to the examples you see in movies or television shows where the FBI gets a warrant to tap the phone line of someone under a federal investigation, except in this instance, we’re tapping the network data.
Making a Case for Network TAPs
The Network TAP (test access point) transmits both the send and receive data streams simultaneously on separate dedicated channels, ensuring all data arrives at the monitoring device in real time - 100% of the time. Because TAPs ensure 100% of the data arrives at the monitoring tool, they are CALEA approved for lawful intercept cases over SPAN ports.
The SPAN port on a switch, also sometimes called a mirror port, will drop packets when ports are oversubscribed and can cause distortions in real time communications like VoIP and video chats. Since the data cannot be trusted 100% of the time, they are not a reliable option for lawful intercept cases.
Download: TAP vs SPAN [Free whitepaper]
Garland Technology + SYNESIS for Lawful Interception
In this instance, the law enforcement agency had already determined that they wanted to use a SYNESIS network packet recorder to ensure high speed data capture of the live network data. A network recorder is a specialized hardware appliance that has filtering capabilities that can be programmed to look for all the data packets associated with a target’s IP address, and then records that information in a digital format. Network recorder tools must have the ability to capture and store extremely large amounts of data, with advanced ones storing amounts in the petabyte range.
The law enforcement agency was looking for a way to properly capture and store data according to warrant parameters, while delivering data directly from the source to the mediation device without any human intervention or packet loss. In lawful intercept cases it’s important to be sure that the traffic feeding the packet recorder adheres to specific regulations providing clear access to all data without any loss of information or impact on the network being monitored.
That’s why the agency turned to Garland. We have a long standing relationship with Toyo and have worked with their SYNESIS tool many times. We were able to deliver an integration solution that combines Garland’s Network TAPs that deliver a 100% complete full-duplex copy of network traffic without packet loss, to the SYNESIS network packet recorder. SYNESIS is the only solution available in the market today that can record and collect 100G traffic without losing a single bit. Using TAPs instead of SPAN ports ensures that the packet recorder didn’t sacrifice high fidelity lossless packet capture performance, regardless of the network speed.
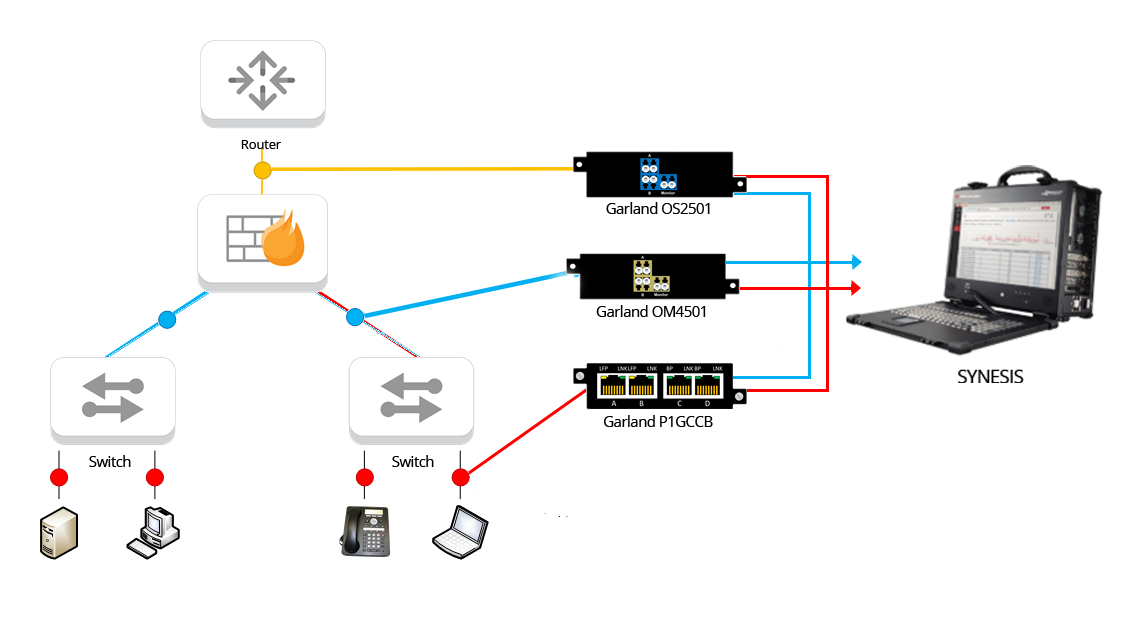
The integrated solution provided the law enforcement agency with two critical components, the TAPs and network recorder appliances, both of which are needed for successful lawful interception. If the solution were unable to access and record data completely at network speeds up to 100G, it would compromise the integrity of the surveyed data. And more importantly the incomplete data captures likely wouldn’t hold up in court.
It isn’t every day we get to collaborate on such interesting cases. It’s solutions and applications like these that make my job fun. Now if I only knew what cases they were using our TAPs to help solve, that would be really interesting!
Looking to add a visibility solution to your next deployment, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do!