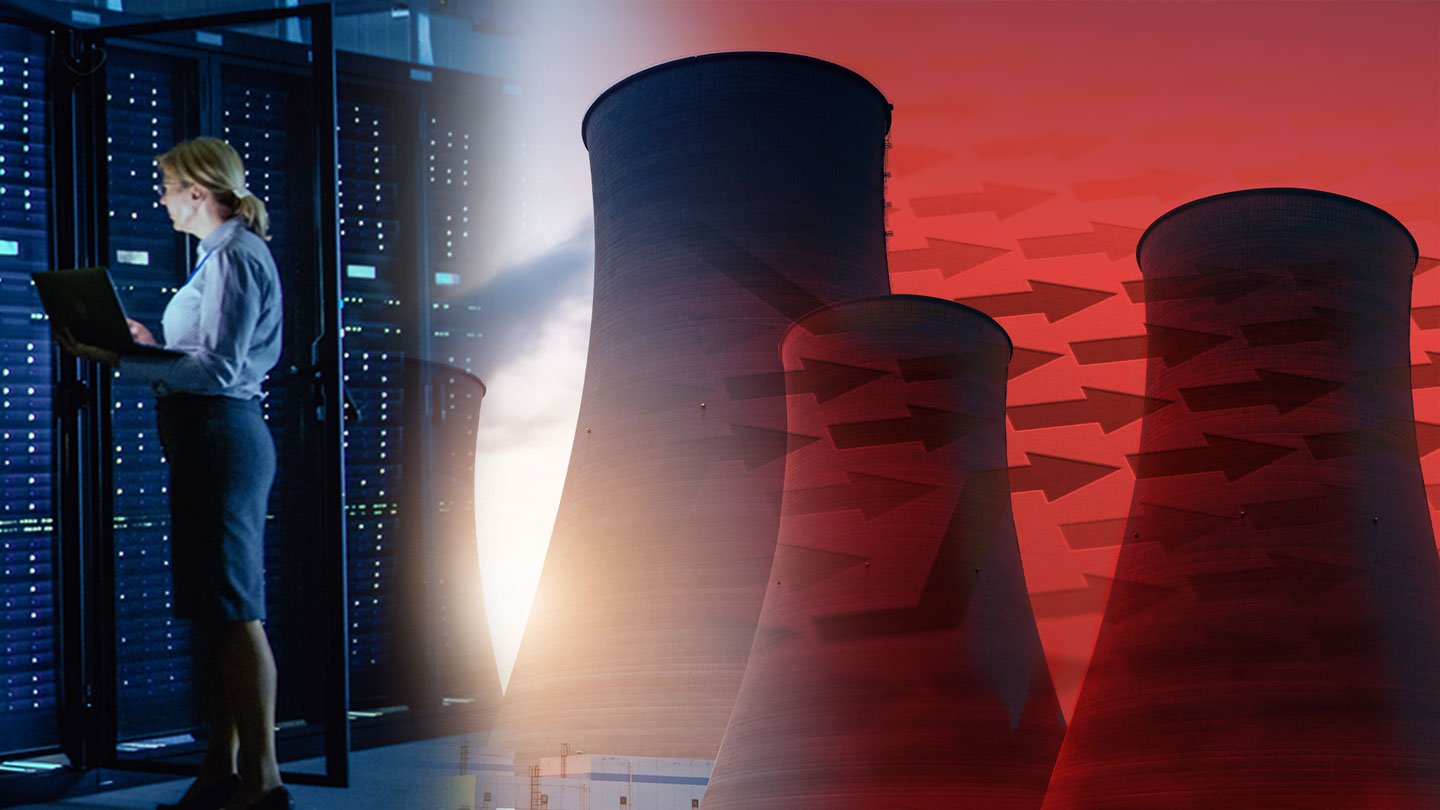
How to Provide Secure Visibility in Manufacturing Networks
Background Today’s critical infrastructure industries include the manufacturing and distribution of goods such as aerospace and defense, electronics, chemicals, pharmaceuticals, automobiles, and food...