
To satisfy the ever-more-specific demands of consumers, network professionals must rise to the challenge of building the most flexible, user-friendly systems possible. In order to make this happen, administrators must be ready to make the leap from the physical to the virtual.
Today, the name of the game is software-defined networking (SDN).
In essence, SDN permits the manipulation of traffic and data flow from a single dashboard, even if users' physical connections to the network are spread out over a number of remote locations or achieved through a wide variety of hardware devices. But as technology advances and users' needs evolve along with it, SDN will need to take steps in order to realize its place as the industry standard.
So, what will the future of SDN look like?
The Roads are Getting Wider
Due to increasing proliferation of mobile, wireless, video content, and the broadened scope of network connectivity enabled by the “Internet of Things,” administrators will be compelled to make the jump to 100 gigabit deployments to keep from falling behind.
By Necessity, Automation Supplants Hands-on Control
The SDN market is soaring: BCC Research estimates a global revenue jump from $2.4 billion this year to a stunning $56 billion by 2020. This sounds like wonderful news, but networks will require more intelligent management tools to support–and justify–the switch. The 100G future is one in which manual network control will no longer be sufficient.
Agility, Agility, Agility
Converting from physical to virtual network controls doesn't happen at an even exchange rate: a single physical function could be replaced by not just one but numerous virtual functions. This is possible through the virtual environment's wide support for cloud and remote-based collaborations. What does all of this mean? A new, much finer level of customization will be achievable for administrators, and customer support can be provided more quickly and cheaply than ever. In a word, agility is efficiency.
There are still very real challenges here in 2016, however, as a number of open questions loom over the landscape of SDN implementation.
Current Roadblocks to SDN Efficiency
One expert from monitoring firm Dynatrace sees most firms as still being a few years away from developing a new platform of apps and tools that will enable an automated SDN standard that's dynamic and nimble. In other words, the software-defined model may not yet be ideal for those who aren't on the cutting edge.
Because SDN will create new interfaces, integrating them requires that infrastructure experts take a possibly uncomfortable leap beyond the current bounds of common best practices. To put it another way? Fortune will favor the bold.
So, what's a firm's smartest move here and now? The industry consensus remains that the big switch to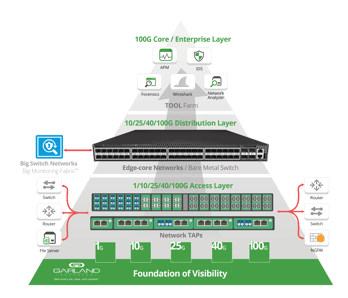 SDN ought to be a top priority. Big Switch Networks, a Garland technology partner, doesn't consider expanded SDN implementation to be a hope for the future—they've made it a point of emphasis in the present.
SDN ought to be a top priority. Big Switch Networks, a Garland technology partner, doesn't consider expanded SDN implementation to be a hope for the future—they've made it a point of emphasis in the present.
Regardless of speed or circuitry, a passive Garland TAP can be integrated with Big Switch's SDN solution, which is controlled through a single virtual platform. This unified solution streamlines programming, security protocols, and controller updates, permitting network professionals to spend less time configuring and more time contouring traffic and monitoring data in real-time.
Big Switch Networks has the tools to make the SDN transition a reality; and, when connected via the proper network TAPs, SDN adopters can ensure their out-of-band monitoring solutions see every bit, byte, and packet® of network traffic.
If you want to learn more about the promises of SDN, NFV and the importance of maintaining 100% network visibility as you make the transition, download our free white paper, Architecting Data Centers for SDN and NFV - In 40G and 100G Environments

