

Nearly all cyber attacks must cross the network, so extracting security-relevant data from network traffic is essential across a wide range of security operations. As teams are moving to the cloud, they lose physical access to applications that previously were housed in the data center. Just as traditional network test access point (TAP) and packet broker solutions fuel monitoring tools traffic from across the network, a solution is needed to continue to feed these tools when there is no longer physical access to applications that now reside in the cloud.
Realizing that organizations need a solution that will provide total network visibility, whether the workloads are on-prem or in the cloud, we released a flexible, cost-effective solution that can be scaled over time.
Some organizations moving to the cloud think that the solution is to rip and replace tools to gain cloud visibility. That's not the best solution at all. Garland Prism's next-gen agent technology can acquire, process, and distribute cloud packet traffic to our traditional high-performance network test access points (TAPs) and packet broker solutions. Garland Prisms is capable of tapping, filtering, and distributing cloud packet traffic to any IP address in-cloud or on-prem. Garland Prisms then sends the tapped traffic to PacketMAX™: Advanced Aggregators through VXLAN or GRE tunnels. The PacketMAX terminates the tunnel and distributes traffic to any number of on-prem tools.
The Garland Prisms solution provides flexibility to organizations to continue with their existing security infrastructure. The solution is affordable, easy to deploy, simple to use, and offers a scalable way to capture network traffic, thus reducing organization risk. 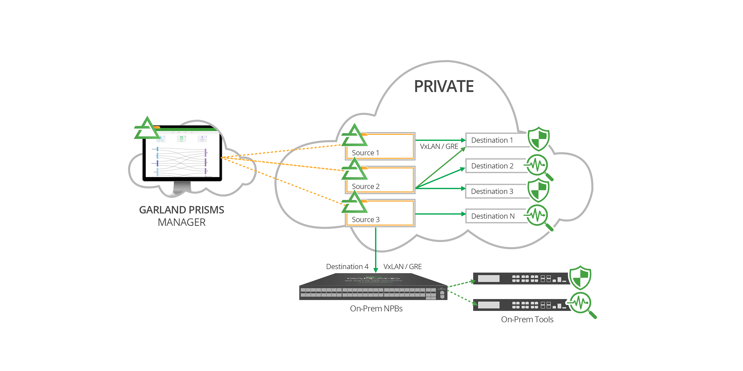
Garland Prisms captures and orchestrates cloud packet traffic from cloud provider infrastructure, such as Azure VTAPS, AWS, cloud firewalls, and cloud workloads including VMs and containers.
Garland Prisms' Service Processor (PSP) prepares packet streams for distribution to a Garland Technology NPB for seamless integration with existing infrastructure. The PSP is container-based and infinitely scalable; it sits inside your cloud subscription, which maximizes security while minimizing impact on resources and exit charges.
Garland Prisms distribute cloud packet traffic to any team, tool, or process. The same source packet streams can be replicated to multiple destinations to save cost, computer overhead, and management strain. Full packet streams can also be replicated for storage, monitoring, and compliance needs.
Through the use of Garland Prisms VxLAN/GRE, organizations can feed the traffic into Garland's PacketMAX packet brokers to get full control over traffic behavior, (e.g. load balance if scale is an issue) and create flexibility for aggregation and re-generation (e.g. feed multiple on-prem appliances).
Looking to add visibility to your cloud deployment, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do!
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.