With today’s compliance landscape and your requirements as a business, you can’t afford to have any holes in your network design. Whether you’re leveraging SPAN ports or network TAPs, it’s critical that your monitoring and security tools and applications are able to completely capture your network traffic data.
Network engineers and managers alike need to think critically about the limitations of conventional data-access methods as well as the use of SPAN technology and port mirroring.
It’s not that a SPAN port has no use in the design of a network. There are certainly situations and environments in which port mirroring works great and gets the job done. But, given that managed switches are an integral part of any network infrastructure, you must understand the limitations of these devices. Be incredibly careful not to introduce a point of a failure on the network, or should the network go down, the security and analysis applications you’ve invested heavily in will no longer be capable of doing their jobs. In these moments when intrusion detection and prevention systems are down, you’re leaving your network open to a data breach.
In addition, overused SPAN ports tend to drop frames because LAN switches are designed to groom data (from adding delays to changing timing), extract bad frames, and ignore all layer one and two information.
"The switch treats SPAN data with a lower priority than to-port data...the best strategy is to make decisions based on the traffic levels of the configuration and when in doubt to use the SPAN port only for relatively low-throughput situations." -Cisco
The way in which SPAN ports are typically implemented makes them incapable of handling FDX monitoring and analysis of VLAN. Understanding what you are able to monitor is essential to designing a successful network.
The potentially limited network visibility of a SPAN and its lack of security in transporting monitored traffic through your network could be a risk to your business from a Data Security Compliance perspective. In a court of law, these shortcomings may be identified as impermissible flaws, leading to costly fines.
When implemented properly and used in an environment in which it will never oversubscribe, a SPAN port is a resourceful network device. But, as 10-Gigabit environments become more common, the SPAN simply won’t suffice. Ensuring complete network visibility requires the use of a network TAP.
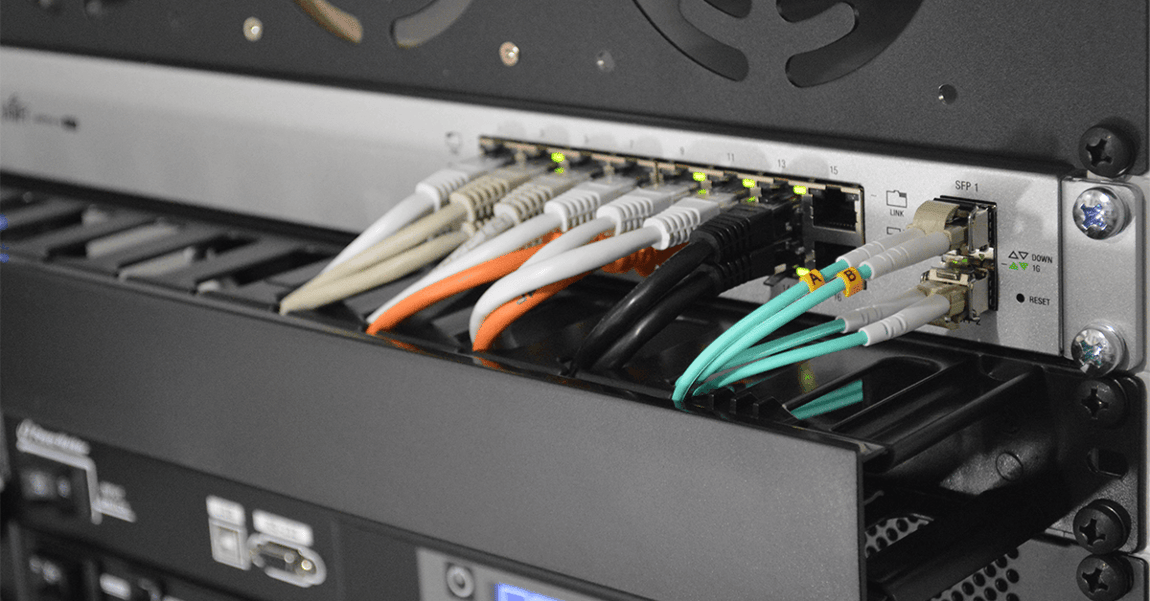
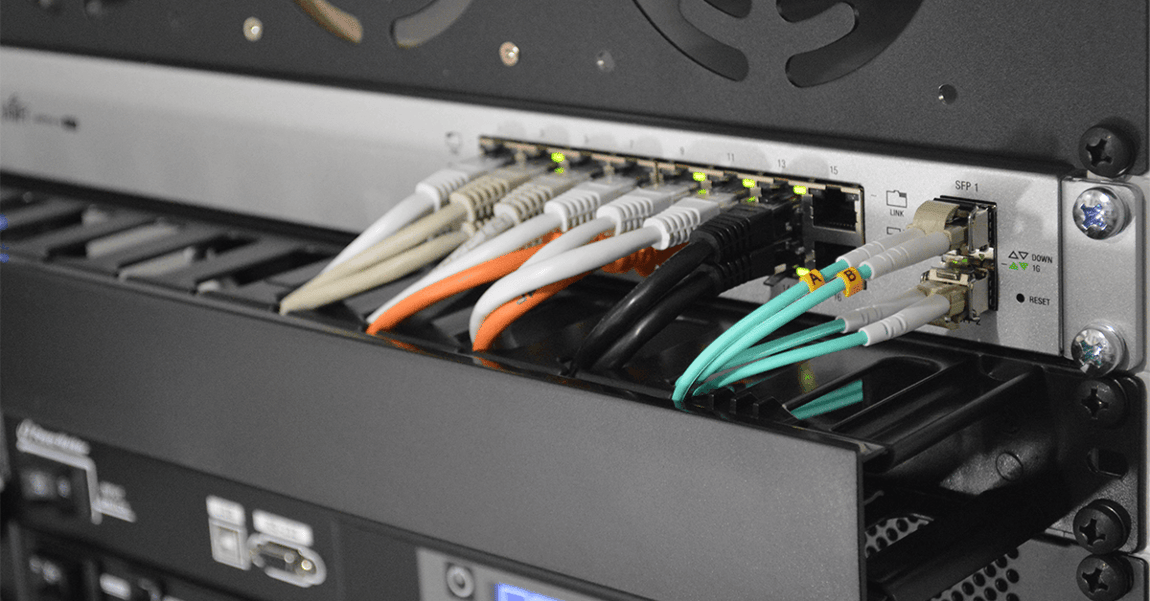
A TAP is completely passive, does not drop packets – regardless of bandwidth – and doesn’t have setup or command-line issues, thereby ensuring complete copies of your network traffic. TAPs also don’t cause any distortion, even on FDX and full-bandwidth networks. As for your network security, network TAPs cannot be hacked by intruders, as they are not addressable devices.
So, stop choosing to use SPAN ports simply because it’s been a common practice, and start considering a device that ensures the function of your in-line appliances and keeps your network safe.
Looking to add a visibility solution to your next deployment, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do!
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.