

Today’s complex networks require hardware and software vendors to work well together to provide solutions that meet the customers’ needs. As a manufacturer of network TAPs and packet broker solutions, Garland Technology knows that enterprises, service providers and government agencies worldwide are likely to have network visibility and access tools from many different vendors in their networks.
That’s why we like to highlight how Garland Technology can work with your existing network packet broker infrastructure, to provide added visibility and ROI to existing investments.
By following network visibility fabric best practices, you can breathe new life into your existing packet brokers through:
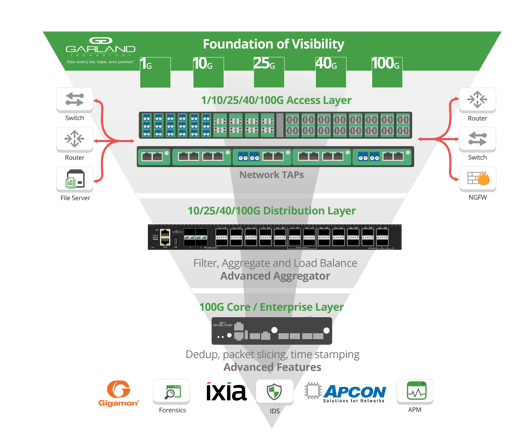
Access Layer: A reliable access layer composed of network TAPs is a critical foundation of all visibility fabrics.
Aggregation Layer: Adding an aggregation layer to your existing core can provide cost savings and improved efficiency.
Advanced Packet Manipulation: Adding a standalone platform extends your feature set, while taking performance burden off the packet broker.
Inline Security: Adding bypass TAPs and hybrid NPBs with inline capabilities secure your deployment from malicious threats.
With an upgrade to multimode 40G, you need to decide how best to provide visibility and access to the new links. While simply replacing everything from the cabling all the way up to the tools to accommodate 40G speeds, may be your first thought, that may not prove to be the solution. For instance, certain monitoring and security tools that you currently use may not support those higher speeds, or the additional purchase could be very cost prohibitive.
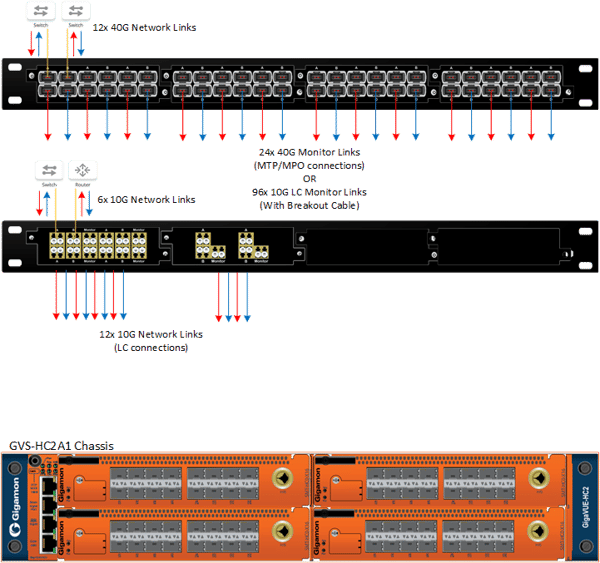
In this example, when upgrading to Multimode 40G links, the solution uses cables with MTP®/MPO connectors instead of LC ports. This will then require a TAP with an MTP/MPO connection. The 10G multiple mode links will require TAPs with LC connections.
Here, the Gigamon HC2 packet broker is modular, allowing it to support multiple types of media connections in different densities. However, with only 4 module bays, a single appliance will not be able to support all the connections required.
2.png?width=600&name=Aggregation%20layer%20surround%20(Packetmax)2.png)
By adding in Garland Technology’s PacketMAX™: Advanced Aggregator, the tapped traffic can be aggregated together to fully utilize each monitor link. Instead of requiring the Gigamon packet broker to support multiple under-utilized monitor links, the Advanced Aggregator allows the packet broker to make the most out of each of its ports. Less ports on the packet broker will be needed, and less expensive modules/licenses will be required, which will save the customer money and extend the lifespan of the packet broker.
With the addition of the PacketMAX™: Advanced Features for de-duplication, packet slicing, GRE tunneling and timestamping, licensing fees and processing overhead are also significantly reduced.
Through our full platform of network access products, Garland Technology adds value back to your investment, allowing you to easily upgrade existing speeds and save on new tools, create scalable solutions for future growth, and make more effective use of NPB licenses and ports.
Looking to add additional traffic aggregation, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do.
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.