

Network visibility fabrics, a combination of network TAPs, network packet brokers, aggregation devices, and bypass devices, play a critical role for network performance management and security operations.
Network requirements are becoming more complicated with each passing year, as more data is flowing across networks, across a wider area, and at higher speeds. This has led to an increased need by enterprises, service providers, and government agencies to require greater visibility into the network to understand what is going on. Enter in the rise of the network visibility fabric to provide a complete view into your network.
Let’s explore the network visibility fabric in more detail, starting with the foundation: the Access Layer.
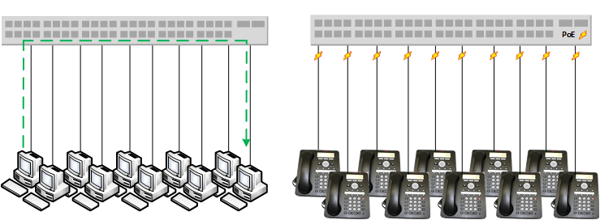
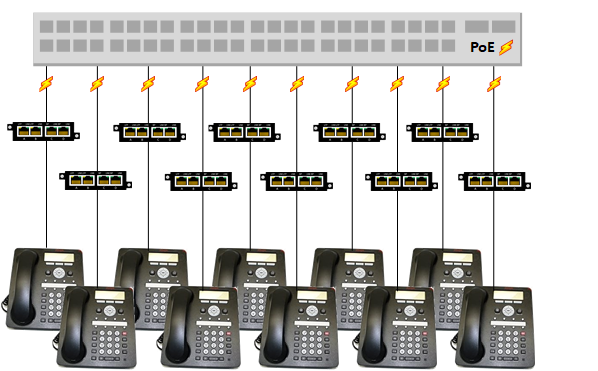
The access layer of a network visibility fabric is where traffic is pulled from the production network. The access layer usually consists of 100M or 1G copper network links, where switches directly connect to end point devices and allow these devices to communicate with each other, and may also provide "Power over Ethernet" to power small devices.
“EMA recommends that enterprises use TAPs as much as possible in the access layer to avoid network performance impacts and assure packet fidelity.” It seems as though the well-documented use cases for Network TAPs are making grounds, as 83% of current network visibility fabrics make use of TAPs for at least half of the fabric access layer.
Network TAPs will provide 100% visibility for out-of-band monitoring tools, as the fabric will mirror the traffic from various segments of the network. This traffic can be sent to monitoring tools like Wireshark, network analyzers, DPIs, and lawful intercept applications.
For inline security use cases, like firewalls and intrusion protection, the fabric will redirect production network traffic to analysis tools and then return the inspected traffic back to the production network. By using bypass TAPs for these inline applications, the network remains protected, and the inline tool does not create a point of failure for the network.
Traffic doesn’t lie, so to get to the bottom of an investigation of a threat or an anomaly, you need to have a complete copy of the network traffic, and using a reliable Network TAP is the way to ensure that.
[If you’re interested in learning more about the principles behind a well-designed network visibility fabric, download Garland’s latest whitepaper from the analysts at EMA: Best Practices for Building a Network Visibility Fabric.]
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.