Garland Technology Products
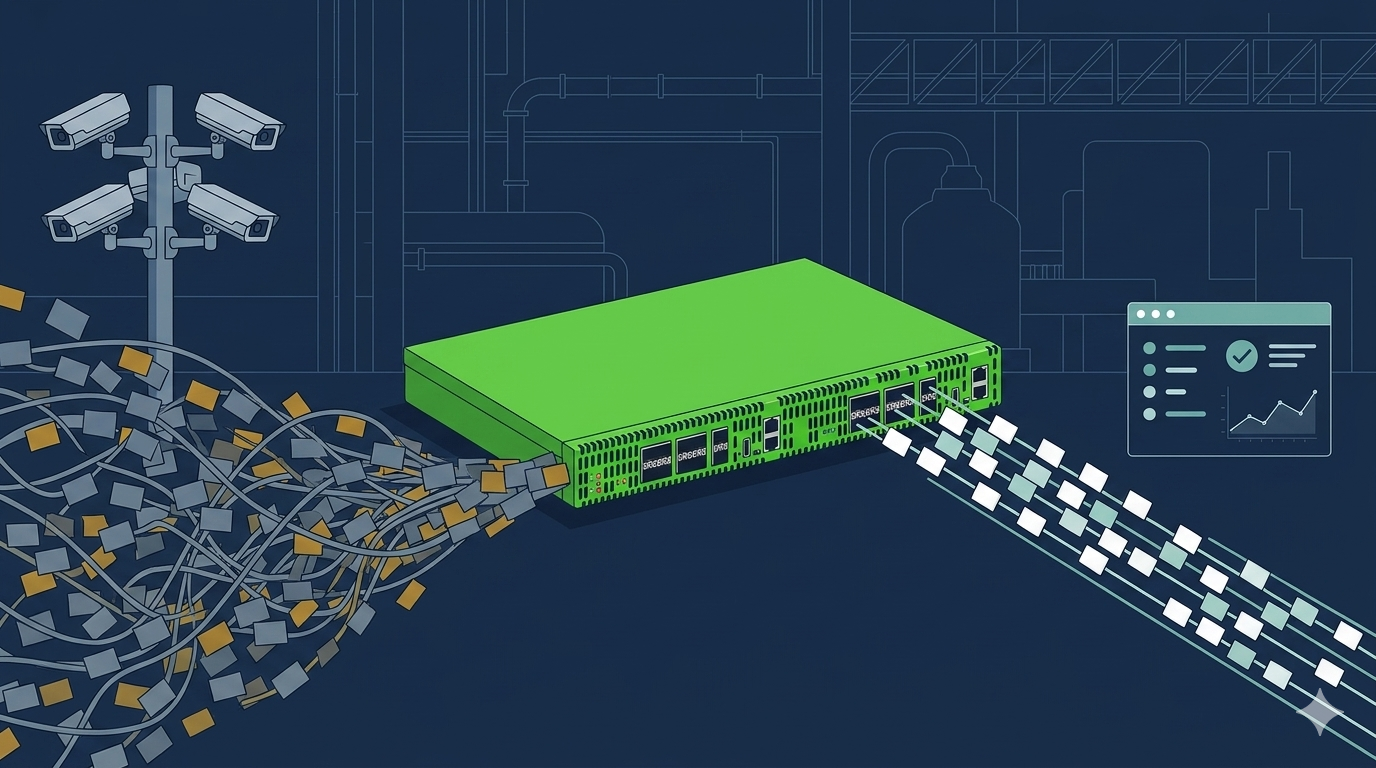
Garland Technology ensures complete network visibility by delivering a full platform of network test access point (TAPs) and packet broker products.
Visibility Solutions
Garland Technology is committed to educating the benefits of having a strong foundation of network visibility and access. By providing this insight we protect the security of data across your network and beyond.
Resources
Garland Technology's resource library offers free use of white papers, eBooks, use cases, infographics, data sheets, video demos and more.
Resources
Read AllBlog
The TAP into Technology blog provides the latest news and insights on network access and visibility, including: network security, network monitoring and appliance connectivity and guest blogs from Industry experts and technology partners
Partners
Our extensive technology partnership ecosystem solves critical problems when it comes to network security, monitoring, application analysis, forensics and packet inspection.
Contact
Whether you are ready to make a network TAP your foundation of visibility or just have questions, please contact us. Ask us about the Garland Difference!