Handle Growing Network Demands with Traffic Aggregation
Garland Technology helps organizations streamline their networks with reliable network traffic aggregation solutions. By consolidating high volumes of network links and speeds, we ease the workload on IT teams, improve data flow efficiency, and ensure monitoring and security tools operate at peak performance through 100% real-time traffic visibility - all while keeping costs under control.

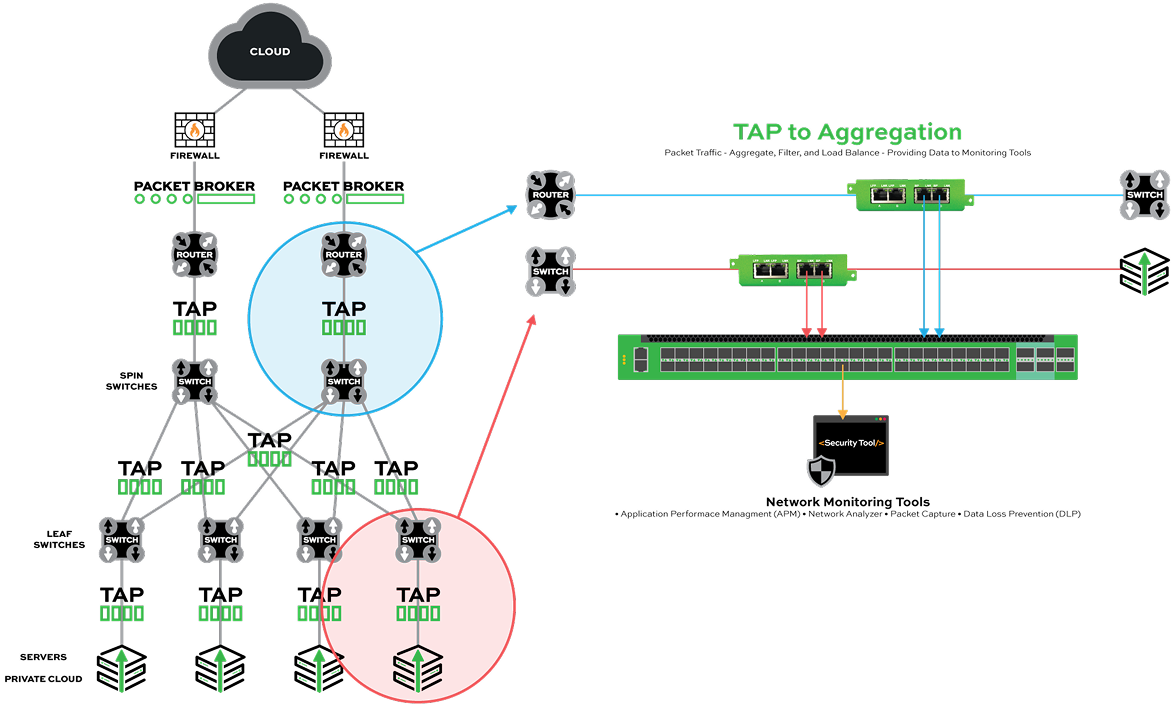
How Traffic Aggregation Supports Hyper-Scaling Network Traffic
As networks evolve, IT teams face growing demands to manage massive traffic volumes from users, the internet, and remote sites. With speeds increasing from 1G to 10G, 25G, and 100G, scalable traffic aggregation solutions from Garland Technology can accommodate your existing infrastructure and also prepare future growth. Network aggregation consolidates links and speeds into a manageable number of ports, so your organization can
- Aggregate TAP or SPAN ports for higher utilization. Combine traffic from multiple ports into a single feed, ensuring tools are fully utilized and no bandwidth is wasted, vs. dedicating individual monitoring tools to each TAP or SPAN port.
- Improve monitoring and security tool efficiency. Traffic aggregation reduces redundant data, so threat detection and performance monitoring tools can focus on actionable traffic.
- Reduce the per-port cost of expensive Network Packet Brokers (NPBs). Fewer ports minimizes the need for added hardware, lowering costs while managing the same volume of traffic.
- Maximize existing investments. Aggregate high-speed links and feed into tools that originally supported lower speeds for continued use without upgrades.
- Scale to handle additional traffic, speeds, and tools. Prepare to accommodate higher bandwidths (100GbE for example), and integrate new monitoring or security tools as needed.
Evolving Beyond the Traditional 3-Tier Network Visibility Model
The traditional 3-tier network visibility model, designed to enhance monitoring efficiency, is becoming outdated as network and tool complexity grows.
To address these challenges, IT teams are adopting a new 4-tiered visibility model that incorporates an aggregation layer to improve efficiency and scalability
The 4-Tier Solution:
Enhancing Efficiency with an Aggregation Layer
Adding an aggregation layer between physical TAPs and NPBs resolves key efficiency challenges:
- Consolidates low-utilization traffic streams, reducing the number of required NPB ports.
- Pre-filters traffic at Layers 2–4, optimizing NPB performance.
- Reduces budget strain by eliminating costs from underutilized ports
This scalable approach lets organizations maximize network efficiency, reduce costs, and future-proof their infrastructure.