Simplify Network Complexity
Aggregation Solutions
Challenge: How can I simplify network complexity?
Expanding networks who deploy various tools, redundant segments and devices, with data streams being monitored by multiple teams, often find themselves inundated in network complexity. Many companies running a majority of their traffic off of SPAN ports often see a tangled web to manage, leading to SPAN port contention that can result in:
• Slower processing speed
• Loss of data and oversubscription
• Slower MTTR and threat hunting
• IT and Security team data silos
Solution
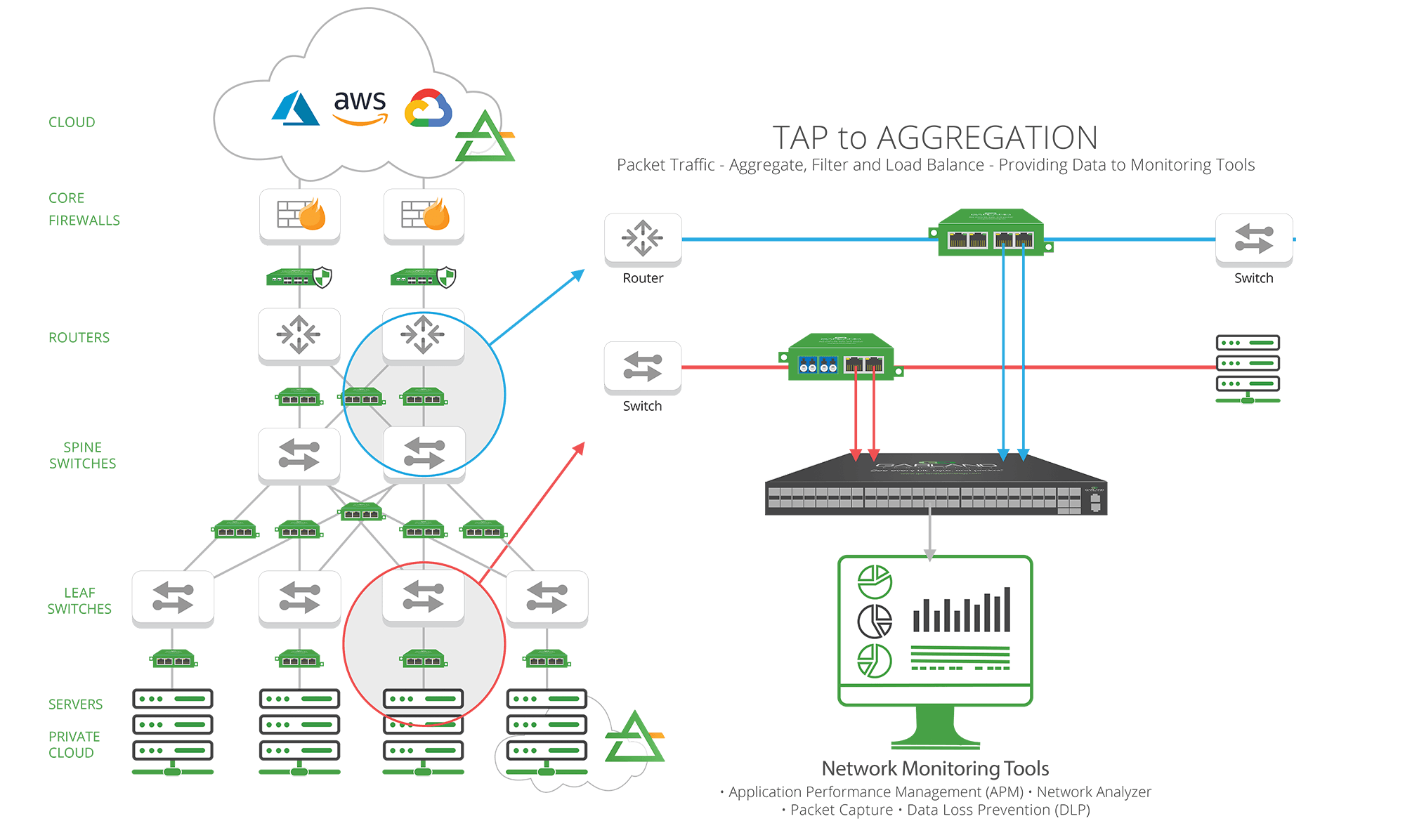
A network visibility fabric of network TAPs and packet brokers can simplify network complexity and provide IT teams enhanced productivity, accelerate resolution of service degradation or downtime and improved IT collaboration, by providing:
• Better data for improved tool performance and added value.
• Easily manage access points in the network to instrument and deploy new monitoring and security tools.
• Aggregated and optimized traffic before it gets to the tools.
• Streamlined data collection for analysis during troubleshooting or security incident response.
• IT and security operations access to the data they need, at the right time.