Axellio
Mitigate Business Critical Vulnerabilities With Complete Visibility
Expecting a PDF?
We created this solution brief as a web page for better mobile optimization and accessibility. If you'd still like a PDF version of this use case, you can download it here:
Packet-Level Insights For Real-Time Data Analysis
Network and security monitoring solutions rely on real-time analysis of network traffic to function effectively. However, as data volume exponentially grows, operation systems become susceptible to traffic overload opening the door to undetected intrusions and increased cybersecurity threat risks. Reliable packet level-visibility is essential to obtain results from your monitoring infrastructure and to understand the root cause of an attack.
Axellio PacketXpress and Garland Technology’s visibility solutions provide complete traffic data for detailed forensics on events while also buffering the monitoring and analysis infrastructure. Capturing and recording data up to 100Gbps sustained with zero packet loss, the solution extends the useful life of the security applications while reducing operating costs.
How it works
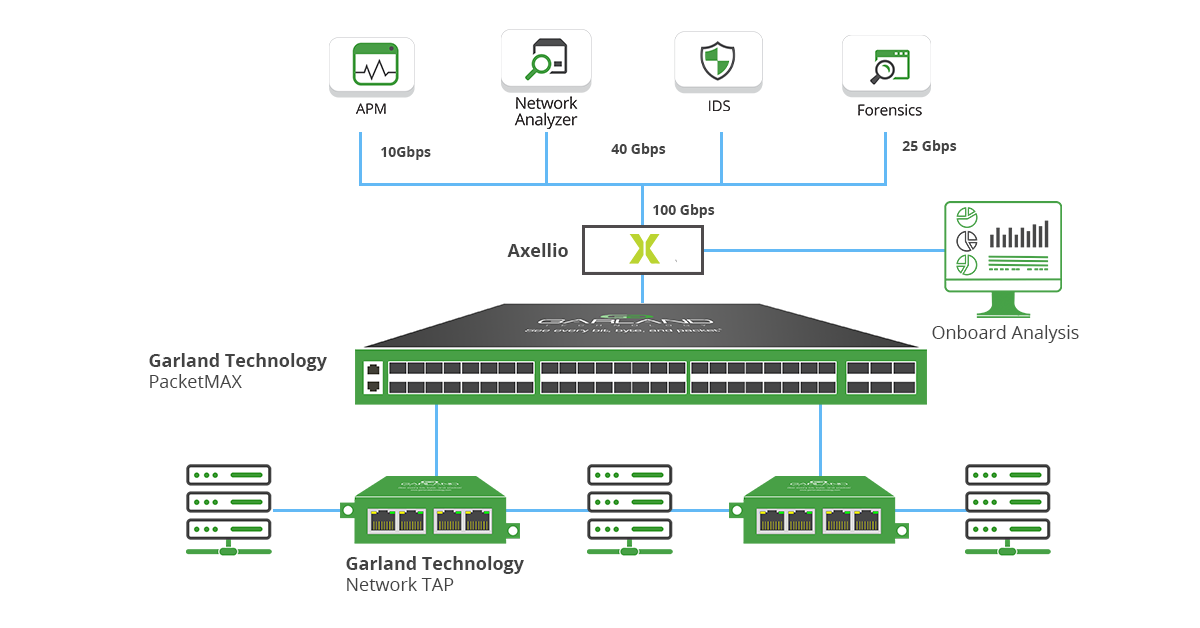
- Garland Technology’s network TAPs copy full duplex packet data from the physical layer.
- Multiple tapped links send the copied traffic to Garland’s PacketMAX Advanced Aggregator, where the data is aggregated, load-balanced and filtered to optimize resource usage.
- The aggregated traffic is captured on disk by the Axellio PacketXpress platform for rate-controlled distribution to other analysis and monitoring applications and for effective in-depth analysis.
IT Ops and Sec Ops Benefits
- Onboard data storage & buffer to smooth out traffic spikes that otherwise overload applications and lead to data loss.
- Zero packet loss at sustained 100 Gbps for reliable real-time analysis that keeps up with traffic growth.
- Duplicate traffic across multiple applications.
- Accelerate time-to-root cause with streamlined analysis and fast access to all pre and post events.
- Replay any traffic anytime for repeated scenario analysis or for validation of deployed mitigations.
- Lowest footprint & cost to performance ratio in the industry.
- Modular hardware & software configuration for extensible storage, memory, and processing.
- Full visibility across your entire network.
Integration Benefits
To eliminate the possibility of blind spots and provide deep packet analysis, the Axellio and Garland Technology solution captures 100% of the packet level data across any infrastructure. Once the data is aggregated and filtered from Garland’s visibility solution, Axellio PacketXpress streamlines the analysis process, shortening time to resolution, providing rapid access to any pre- or post-event data for forensic analysis. Axellio smooths out traffic spikes by distributing captured traffic at controlled rates that would overload monitoring applications and lead to data loss. This extends the useful life of your monitoring infrastructure, shielding from traffic spikes and delaying necessary upgrades.
For root cause and forensic analysis, Axellio PacketXpress also provides fast access to all packets pre- and post-event to quickly determine the mitigation for any security breach.
About Axellio
Axellio Inc. is a leading innovator in high-performance network packet capture, storage, and analysis solutions. Axellio was spun-out in 2018 from an earlier company with a twenty-year legacy of innovation in enterprise IT high-performance storage solutions for commercial enterprise as well as aerospace and defense agencies. Axellio developed a unique solution for the most challenging problem in network and security operations: how to capture packets both economically and reliably for detailed analysis while providing efficient access to the data. For more information, visit Axellio.com.

Garland Technology and Axellio provide packet-level insights for real-time data analysis. Looking to add this solution, but not sure where to start? Join us for a brief network Design-IT Demo or consultation. No obligation - it’s what we love to do.
Increase Zero Trust Effectiveness by Simplifying Your Security Stack
| July 13, 2023
The US government is rapidly transitioning to Zero Trust security architecture. This includes new guidance, reference architectures, and mandates..

Ensuring Federal Cybersecurity Success with Flexible, Compact Flyaway CyberKit Visibility
| August 25, 2022
Recent U.S. Federal cybersecurity initiatives have been put in place to ensure critical infrastructure, whether it's a pipeline, food processor, or..

Ensuring Federal Cybersecurity Success with Flexible, Compact Flyaway CyberKit Visibility
| September 30, 2021
Recent U.S. Federal cybersecurity initiatives have been put in place to ensure critical infrastructure, whether it's a pipeline, food processor, or..
