Millions of industrial devices operate at energy, manufacturing, transportation, mining, and other industrial sites. Comprehensive cybersecurity that focuses on asset visibility proves essential in reducing risk and improving the resiliency of industrial operations. Dragos and Garland are working together to improve cybersecurity and operational reliability while reducing integration efforts and costs.
The Challenge
Traditionally, operational technology (OT) networks were architectured almost wholly separated from information technology (IT) networks. Today, industrial environments have shifted to a more interconnected architecture, enabling cyber threats to reach beyond the traditional IT assets. Thus, cybersecurity teams are being challenged to secure and then manage networks that traverse their entire organization, requiring operational visibility to include the wide variety of OT and IT devices on their networks.
The Solution
Organizations can leverage Garland Technology’s visibility solutions to feed data to the Dragos Platform to help streamline the security of the ICS/OT network infrastructures while helping to avoid operational impacts in legacy systems.
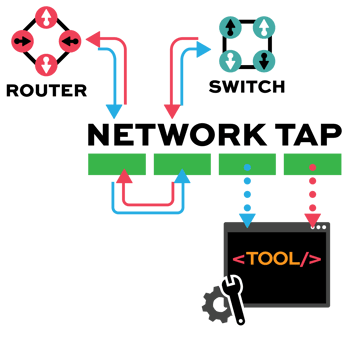
Garland’s passive network TAPs are purpose-built hardware devices that provide essential access in ICS/OT environments. TAPs are available in both fiber and copper models to support all legacy and modern architectures, yet will not add any latency or security risk to the environment. By tapping points of interest throughout the ICS/OT network, security and other monitoring solutions can receive 100% of the traffic to enhance their defense capabilities without introducing new or manipulated traffic to the production network streams.
By deploying the joint Garland and Dragos solution, organizations can centrally visualize the systems, devices, and interactive communications between them. Additionally, they can continuously monitor and detect threats as they occur and use prescriptive workbench tools for more efficient investigations and responses. With this enhanced deep packet level of visibility across critical infrastructures, defenders can protect their operations from potential disruption caused by threats and anomalies while improving their safety, reliability, and cyber resilience across their unique network infrastructures.
TAP -> TOOL
Network TAP Benefits
- Provide complete packet visibility with full-duplex copies of network traffic.
- Ensure no dropped packets while passing physical errors and support jumbo frames without delay or altering the data.
- Support speeds from 10/100M, 1G, 10G, 40G, 100G, and 400G are available in single-mode and multi-mode fiber or copper ethernet.
- Available in Tap ‘Breakout,’ aggregation, regeneration, bypass, and advanced filtering.
- Passive or failsafe – Does not affect the network.
- No IP address or MAC address, and cannot be hacked.
- Advantages of the Joint Solution
- Legacy Architectures
- Distributed Networks
- Proof of concept
- ICS Village video
- Webinar
- Full PDF Solution Brief
• Minimize risks to ICS/OT environments and maintain optimal device utilization by transferring the monitoring demands to systems and devices that are not critical to the infrastructure.
• Reduce network downtime and monitoring solution deployment time with easy inline deployment options that require zero configuration changes to existing infrastructure.
• Comprehensive asset visibility supported by virtual or physical appliance options for deployment within hybrid environments enabling detection of ICS/OT security threats regardless of the infrastructure used.
• Easy configuration and deployment options ensure that network infrastructure reliability is maintained and implementation costs for monitoring solutions are minimized.
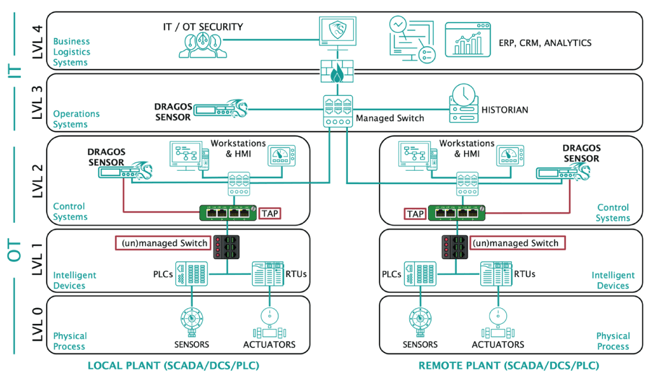
Legacy Architectures
Legacy ICS/OT networks were designed primarily with reliability and safety in mind, evolving business objectives have caused the underlying OT systems to keep pace over the past decade to support newer business requirements. When you start to push legacy equipment to transfer data outside of these proprietary systems, you open the industrial network to security vulnerabilities. The basic architecture below depicts a scenario where legacy networking devices are unmanaged switches (no SPAN option) or managed switches that lack the resources to support SPAN capabilities. Deploying Garland TAPs designed to support 10M/100M/1G between the two network segments will provide the Dragos Platform with at least a baseline amount of data to provide asset inventory, vulnerability management, and threat detection in a single application, making your cybersecurity teams more effective.
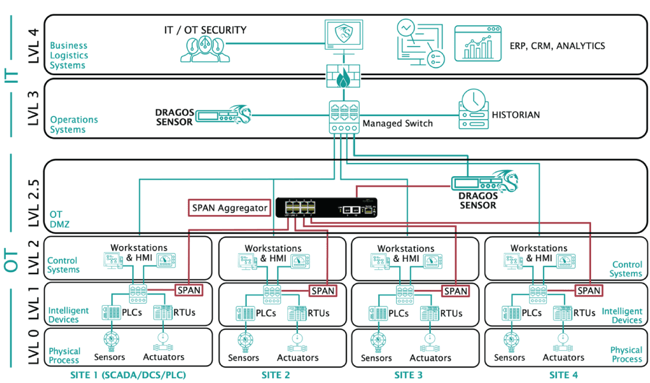
Distributed Networks
As ICS/OT environments get upgraded and modernized, the network switches include features that help support monitoring requirements. For example, port mirroring, also known as SPAN (Switch Port Analyzer), are designated ports on a switch programmed to send a copy of network packets seen on one or more ports to another port, where a monitoring solution can analyze the packets. The basic architecture below depicts a scenario where several site locations have SPAN capabilities; however, the physical location cannot support additional hardware due to space, power, environmental, or budget constraints. Deploying Garland's High-Density Aggregator Network TAPs will allow multiple sites to SPAN their traffic to a single aggregator. The TAPs will then send the data to the Dragos Platform to enable comprehensive asset inventory, vulnerability management, and threat detection view making your cybersecurity teams more effective. Depending on the physical and network configuration, it is also possible to leverage the port pair functionality of the Garland TAPs and implement the device inline, minimizing the load of the existing network devices, and the risk of SPAN packet drops.
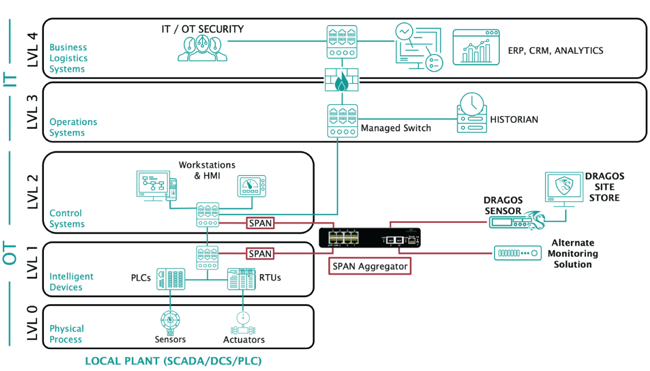
Proof of Concept
With the changing cyber-threat landscape impacting how the management of ICS/OT environments occurs, the need for passive, real-time monitoring is more vital than ever, especially for infrastructures with an abundance of legacy equipment. As with any solution selection process, organizations must traverse through a series of requirements before making a final decision. To ensure that the comparison process for each solution is equal and addresses the essential goals, the basic architecture below depicts a scenario where a proof-of-concept, staging, pilot, or training simulator environment is set up. This environment provides managed switches that support SPAN and a replica of a production environment that mimics where the solution will ultimately monitor and protect. Deploying Garland's High-Density Aggregator Network TAPs allows consolidation of the traffic on the two networks, then sending that data to the Dragos Platform and another monitoring solution simultaneously. This configuration provides a side-by-side comparison of how each solution handles asset inventory, vulnerability management, and threat detection with the same data. It is also possible to leverage the port pair functionality of the Garland TAPs and implement the device inline, minimizing the load of the existing network devices, and the risk of SPAN packet drops.
ICS Village: Gaining Visibility Into Your Critical Infrastructure
Join ICS Village as they demonstrate how companies with industrial control systems gain visibility by deploying OT Security tools with Dragos and Garland Technology. Review how to overcome legacy equipment challenges, aggregate distributed networks, and how to launch a proof of concept design to quickly meet today’s requirements.
Webinar: Achieving Network Visibility in Your ICS/OT Environment
Learn how Dragos and Garland Technology can help you accelerate and mature your ICS/OT cybersecurity programs through asset discovery, streamlining, and complete packet visibility.
Jason Farmer, Solutions Architect at Dragos, Joshua Carlson, Senior Business Development Manager at Dragos, and Neil Wilkins, Garland Technology's EMEA Technical Manager will be discussing changes in ICS/OT environments that driving the need for increased visibility and how together Dragos and Garland Technology provide a simple, scalable, and easy to use solution.
Click to Watch Now






