Reduce Network Downtime
Financial Solutions
Challenge: How to reduce downtime in your network
As inline security devices sit between network segments, managing the risk of downtime is a critical consideration when deploying security tools. Downtime, whether planned or unplanned, can not only impact the functionality of the network but also impacts availability and lost revenue to the company. When deploying inline security tools, security teams commonly face:
• Oversubscribed devices, degrade network performance
• Device failures can bring down segments or the network
• Deploying new technologies into the network
• Scheduling off hour planned downtime for deployments, maintenance and troubleshooting
Solution
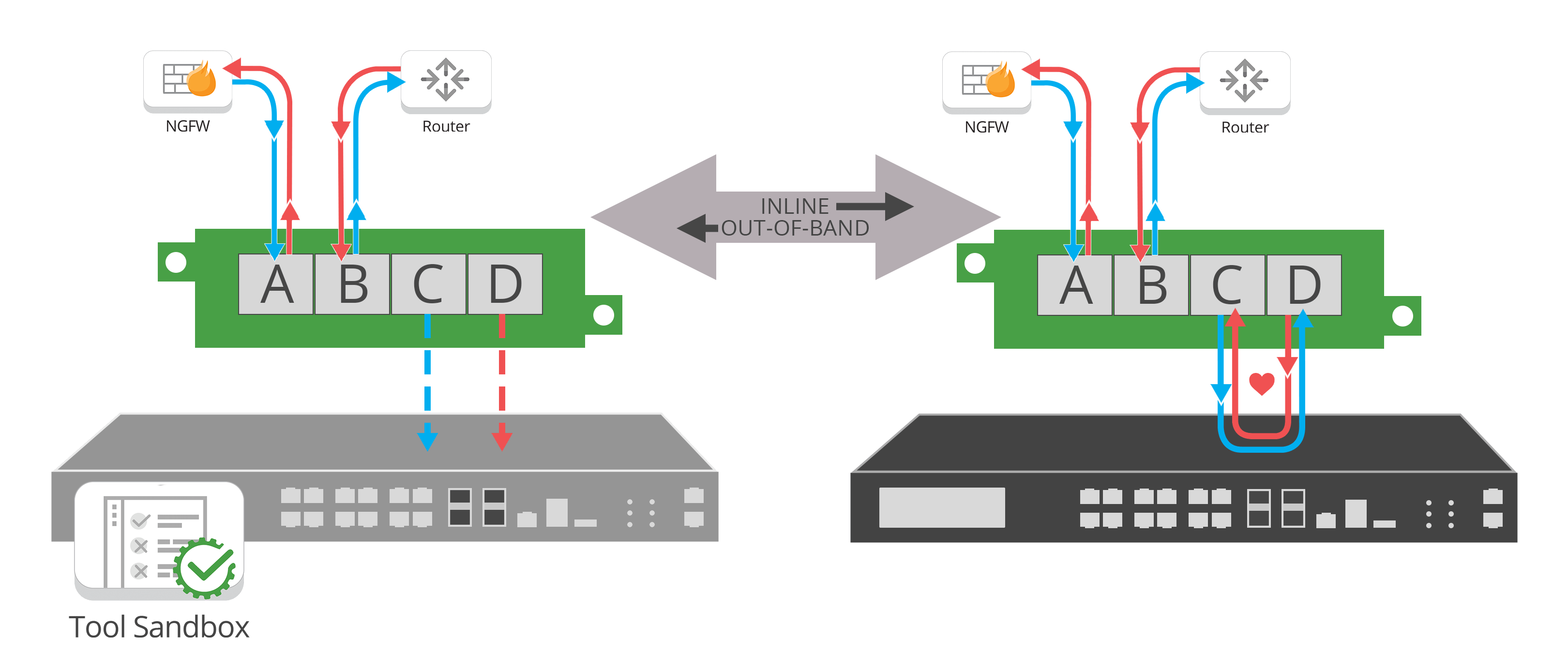
Bypass functionality is essential to preventing inline security devices from causing network performance degradations and downtime. Many appliances have internal bypass capability, but external bypass devices are considered more reliable and offer more features. Extensive use of external bypass devices is a best practice.
Bypass TAP “inline lifecycle management” allows you to easily take tools out-of-band for updates, installing patches, maintenance or troubleshooting to optimize and validate before pushing back inline, offering:
• Administrative isolation - No maintenance windows
• Deployment efficiency - Extend the reach of the same tools into multiple network segments, when used in conjunction with a network packet broker
• Tool Sandbox - Pilot or deploy new tools
In the tense moments of unplanned downtime, a bypass TAP provides expedited MTTR, or problem resolution in the event of a tool failure. By not impacting the overall availability of the connected network, administrators can focus on fixing the tool rather than having to manage the related symptom. A bypass TAP offers flexibility to bypass the tool and keep the network up, failover to a redundant link, or leverage an HA solution, including:
• Operational isolation - Expedited problem resolution of unplanned downtime without impacting general network connectivity
• Network resilience - Flexibility to bypass the tool and keep the network up, or to failover to a High Availability [HA] solution