Eliminate single points of failure
IT Security Solutions
Challenge: How do I eliminate single points of failure in my network?
Our team is tasked with adding IPS active blocking throughout our network on all critical links. Before we deploy these, we want to ensure we aren’t adding additional risk into our security strategy.
Inline tools designed to inspect and block threats in real time, such as Firewalls (NGFW, WAF), Intrusion Prevention System (IPS), and Data Loss Prevention (DLP), must sit on the live network circuit.
Because these Inline tools sit in the live network, the challenge of deploying these tools is to not create a possible single point of failure (SPOF) in the process. SPOFs arise if any of the inline tools become unavailable for any reason such as power loss, traffic congestion or degradation, software or processing errors, which will bring down the link or even the network.
The core challenge is that these inline security tools create a constant tug of war between network security and downtime. Deploying advanced security solutions to inspect and block threats in real time seems like an obvious component of network design. However, each tool you deploy on the live network circuit becomes a new single point of failure for your data center.
Solution
When architecting inline security tools into your network, incorporating bypass and failsafe technology together with network redundancy are three fundamental best practices to avoid costly network downtime, eliminating single points of failure in your network.
Incorporating a bypass TAP provides the ability to manage your inline tool any time without having to take down the network or impact business availability for maintenance or upgrades — ensuring this inline security tool is not a point of failure in the network.
In the case of a failure, a bypass TAP offers flexibility to either bypass the tool and keep the network up, failover to a redundant link, or leverage a high availability (HA) solution.
Bypass TAPs offer the flexibility to take the tool in and out-of-band as shown here:
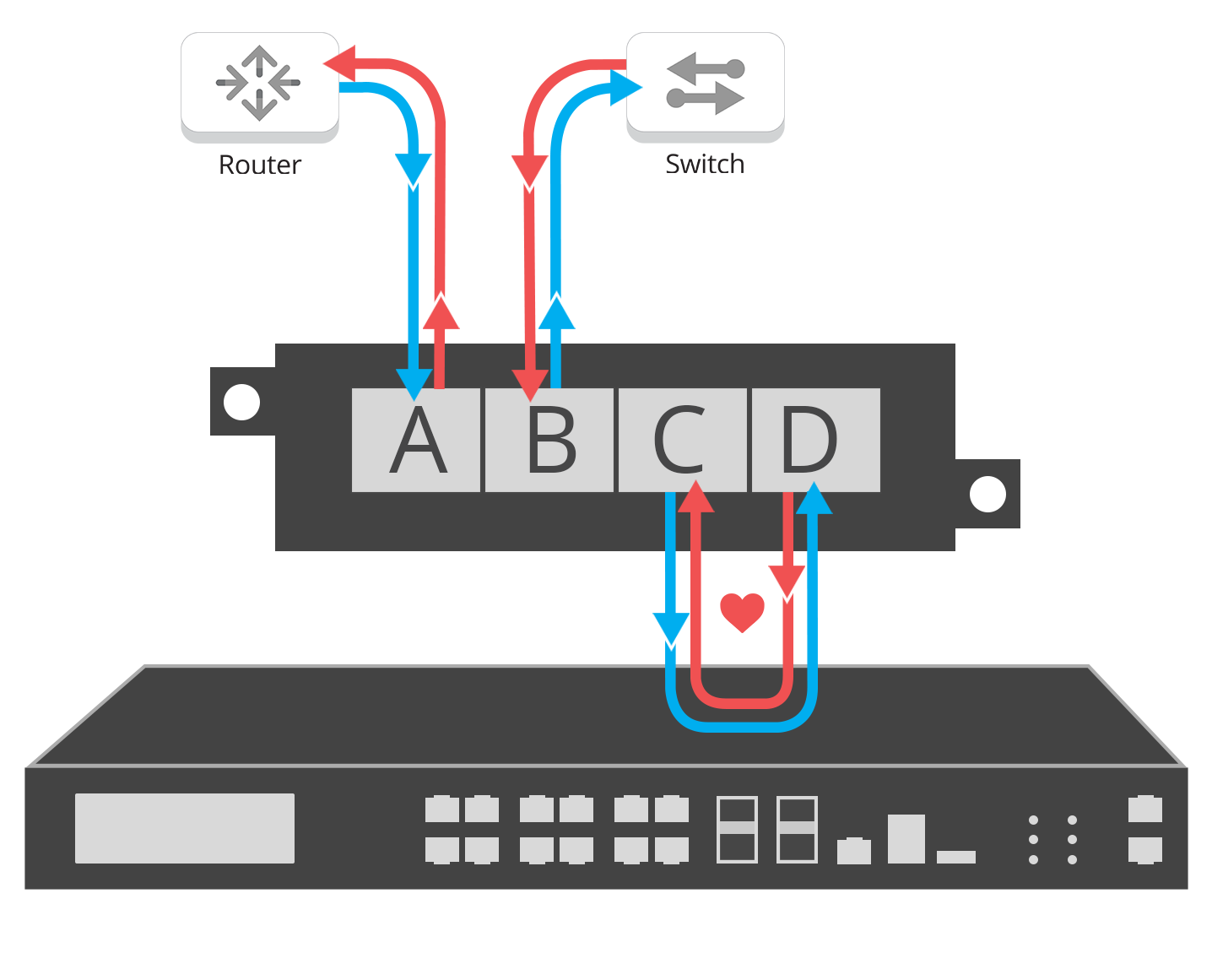
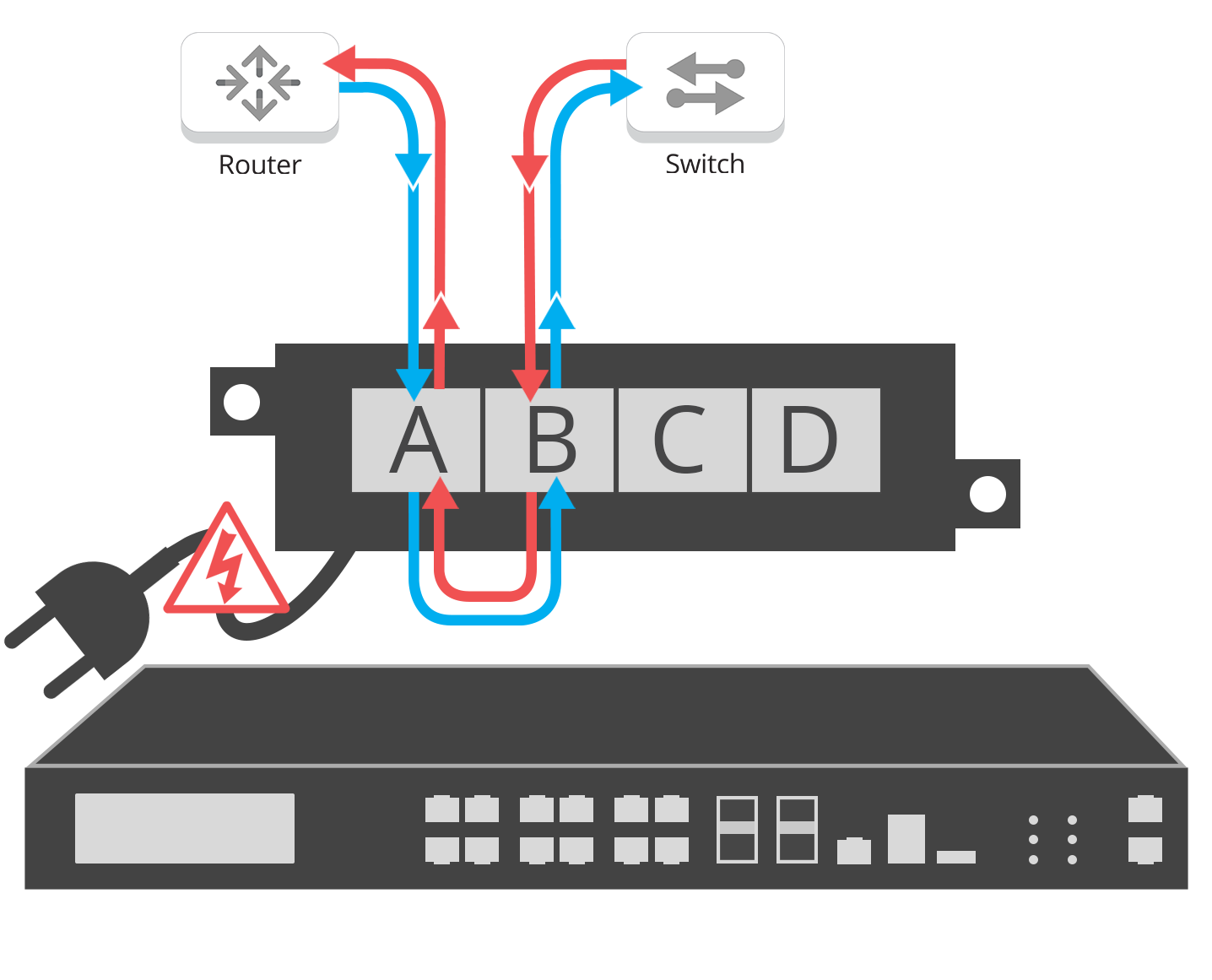
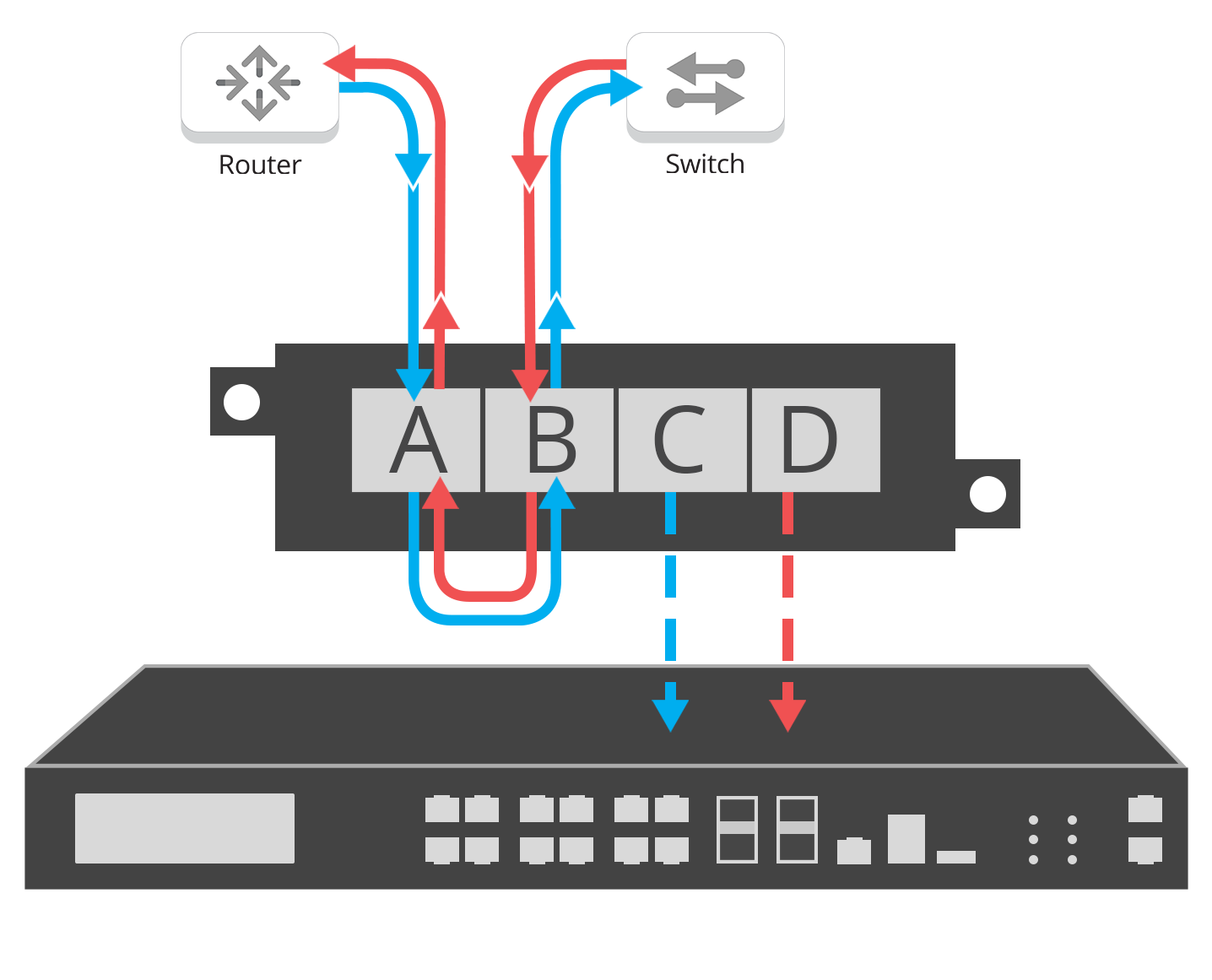
Inline Bypass provides:
• Failsafe deployment of inline tools
• Configurable security tool heartbeats
• Eliminates single points of failure within your network
• Reduce network downtime, with inline lifecycle management
• Operation isolation and tool sandboxing (updates, installing patches, maintenance or troubleshooting)
• No maintenance windows
• High availability (HA) inline deployments adds additional layers of resiliency and reliability
