Security Challenges
Increasing convergence of IT and OT environments has expanded the attack surface and introduced new security risks for critical infrastructure. Older and inherently vulnerable Industrial Control Systems (ICS) that were previously ‘air gapped’ or isolated are becoming increasingly exposed to threats as IT and OT converge. Additionally, as the number of industrial IoT devices has risen dramatically over the past several years, the overall level of visibility for security teams into these assets has decreased, creating easy entry points for attackers.
OT security teams continue to suffer from a growing skills shortage, tight budgets, and are understaffed compared to the IT security teams. Furthermore, as United States and European regulations on OT/ICS tighten, critical infrastructures must find a way to improve their OT security posture with an easy to deploy solution providing visibility across all Purdue Levels.
Key Solution Benefits
• Increased visibility across OT, IT, and IioT to Purdue level 1 where there is lacking existing switching infrastructure.
• Protocol and technology agnostic.
• Illuminates points of IT/OT convergence.
• Reduces risk of misconfigured switch ports.
• Guarantees unidirectional traffic flow with data diode protection.
•Reduce complexity of deployment in distributed networks.
• TAPS do not have an IP or MAC address so are not hackable from a network standpoint.
• Zero hardware subscription fees from Garland Technology.
Garland EdgeLens Solution
Garland’s EdgeLens series is an advanced bypass TAP with built-in packet broker functionality that centralizes network traffic, making network tools more efficient by sharing network traffic with monitoring and security tools. EdgeLens provides visibility for a hybrid configuration of an active, inline network device and out-of-band tools, such as LiveAction. EdgeLens provides identical network traffic streams through the active inline device and to the capture engine of LiveAction LiveWire or LiveCapture. The benefits of both devices seeing the same traffic are:
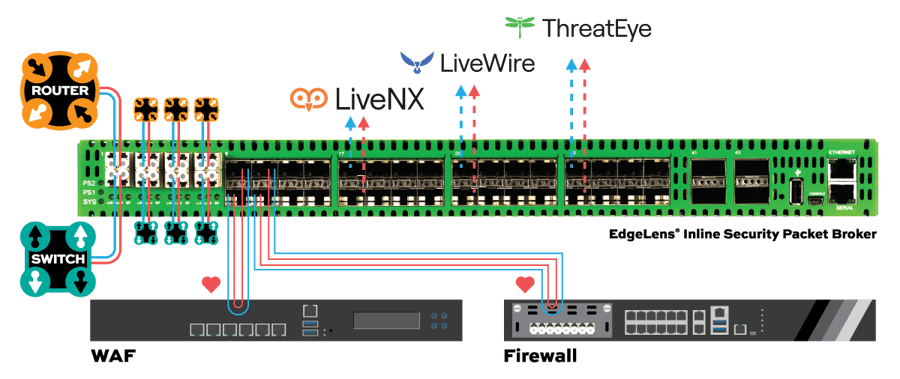
• Correlated data for real-time monitoring and root cause analysis using network packets.
• Historical look back and playback of the network traffic.
• Validating and updating network policy changes and spotting anomalies.
• Network data recording for compliance and security forensics.
• Root cause analysis for application and network related problems.
TAP -> TOOL
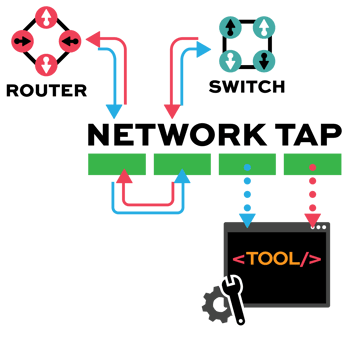
Network TAP Benefits
- Provide complete packet visibility with full-duplex copies of network traffic.
- Ensure no dropped packets while passing physical errors and support jumbo frames without delay or altering the data.
- Support speeds from 10/100M, 1G, 10G, 40G, 100G, and 400G are available in single-mode and multi-mode fiber or copper ethernet.
- Available in Tap ‘Breakout,’ aggregation, regeneration, bypass, and advanced filtering.
- Passive or failsafe – Does not affect the network.
- No IP address or MAC address, and cannot be hacked.
Modern manufacturing, logistics, transportation, and other critical industries increasingly rely on automation to help drive down costs and increase efficiency. With the rise of Industry 4.0 and widespread implementation of IIoT-based automation, organizations are suddenly faced with unique security posture challenges. Today’s automation systems host an array of vendors and legacy (and often outdated) assets. Applications and corporate IT systems must be accessed by 3rd party integrators and consultants greatly increasing the attack surface. You can easily see why exposure to cyber threats, through malicious activity and human error, continue to increase. Organizations must now find creative ways to stay ahead of the hackers and that starts with improving visibility across ICS environments.
Garland Technology and Radiflow each offer costeffective, scalable solutions designed to meet the unique needs of critical infrastructure and industrial networks. Teaming up multiplies the benefits to OT customers.
The initial stage in securing industrial operations involves mapping the OT network, including network topology, modern and legacy assets, devices, ports, and all connections. The result is a virtual model of the complete system, down-drillable to each device. To ensure that Radiflow’s iSID Industrial Threat Detection system has complete visibility and access to network traffic, Garland Technology Network TAPs are deployed as the access method for network traffic at each critical point of interest in the network. Once network visibility is established, iSID can begin to protect against cyber attacks, enforce policies, provide anomaly detection, monitor operational behavior, and perform maintenance management.
- Single Site Deployment
- Multisite Deployment
- JOINT SOLUTION BENEFITS
- Full PDF Solution Brief
- Utility Substation Use Case
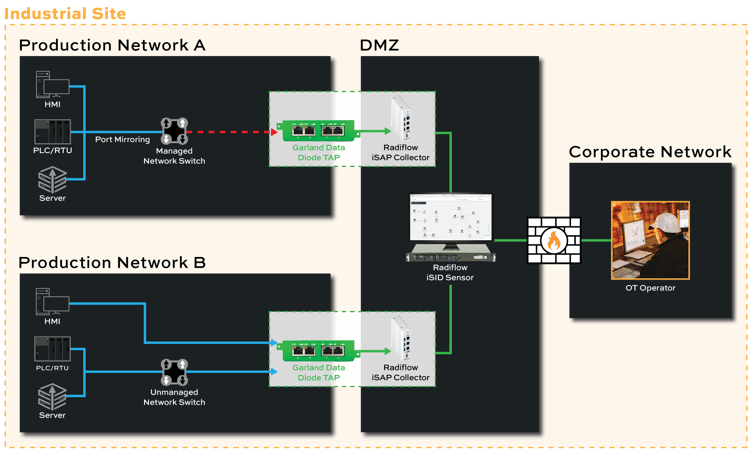
The Garland Network TAP allows for up to 4 links to be tapped and aggregated together to feed the iSID Threat Detection Server in an out-of-band, passive deployment. By using a TAP instead of configuring a mirror port on a Switch, if one is even available, customers will be able to guarantee that 100% of the network packets are delivered to iSID for analysis, while providing unidirectional traffic via the built-in data diode functionality of the TAP.
The Radiflow iSAP Smart Collector is a cost effective, distributed solution that offers a network-wide view of all connected devices and all network traffic for threat detection at a central site. Installed at each remote site, iSAP receives all LAN traffic from the Garland Network TAP and filters out much of the irrelevant traffic data, leaving intact the SCADA traffic. Each iSAP securely connects to a centrally located iSID Threat Detection server, where corporate-wide network and device activity is analyzed.
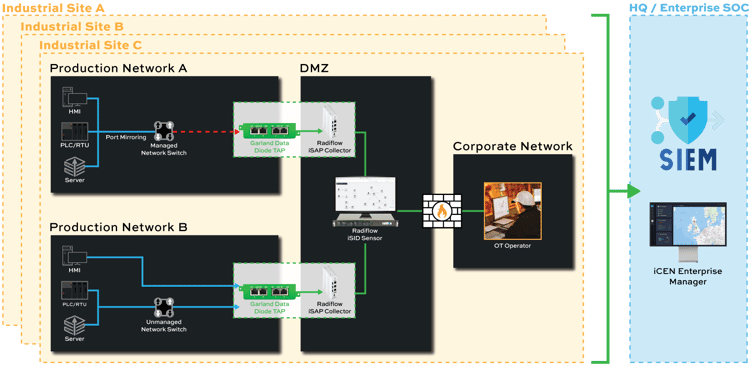
Radiflow iCEN simplifies and streamlines the monitoring and management of multiple instances of the Radiflow iSID Industrial Threat Detection System. From a single iCEN, users are able to observe the status and activities of all iSID instances across the organization, obtaining a unified view of each site’s OT assets with easy drill-down to detailed information. iCEN also enables single-click provisioning of up-to-date cyberattack detection signatures and user-defined rules to multiple iSIDs, enabling improved response time and detection of new threats across the organization.
• Automatic learning of topology and operational behavior
• Flexible deployment models
• Non-intrusive network operation
• Guarantee 100% full duplex network traffic with no packet loss
• Low false-alert rate
• Unidirectional transmission of network traffic
• Products engineered for extreme OT environments including heat and vibration, wired DC power is also available
• Maintenance of network integrity for industrial network monitoring without exposing additional risk
- How It Works
- Bypass TAP Benefits
- Full PDF Solution Brief
- How It Works
- How It Works
- How It Works
Bypass manages the availability of inline tools, preventing a single point of failure in the network by “bypassing” the device in the event it fails or needs to be updated. Reducing network downtime. Bypass is unique to the other TAP modes, as it is an inline use case not out-of-band.
• Keep up with Federal security mandates
• Expedited problem resolution
• Ability to pilot or deploy need security tools
• No maintenance windows
• Simple configuration ensures a quick set-up
• Zero subscription fees so O&M expenses don’t increase
■SOLUTION EDGESAFETM BYPASS TAP
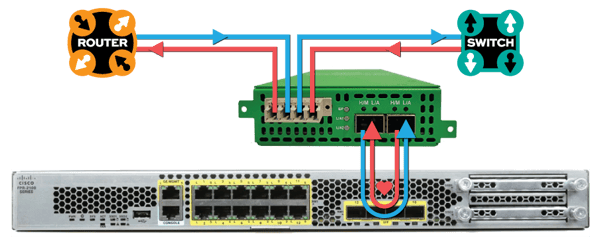
• Install a Garland Technology Bypass TAP between Cisco Firepower and the network
• Bypass TAP manages the availability of Firepower at any time without having to take down the network
• Bypass TAP continuously checks the health of Firepower with heartbeat packets and the Bypass TAP will bypass Firepower to keep the network up-and-running in the event Firepower becomes unavailable
| PROBLEM 1 PORT FAILURE | ||
|
■WITHOUT TAP • The network |
|
■WITH TAP • Uptime • Tool is bypassed while it is being updated |
| PROBLEM 1 PORT FAILURE | ||
|
■WITHOUT TAP • The network |
|
■WITH TAP • Uptime • Tool is bypassed while it is being replaced |








