Dropped Packets
TAP vs SPAN
Challenge: My security tool is missing packets
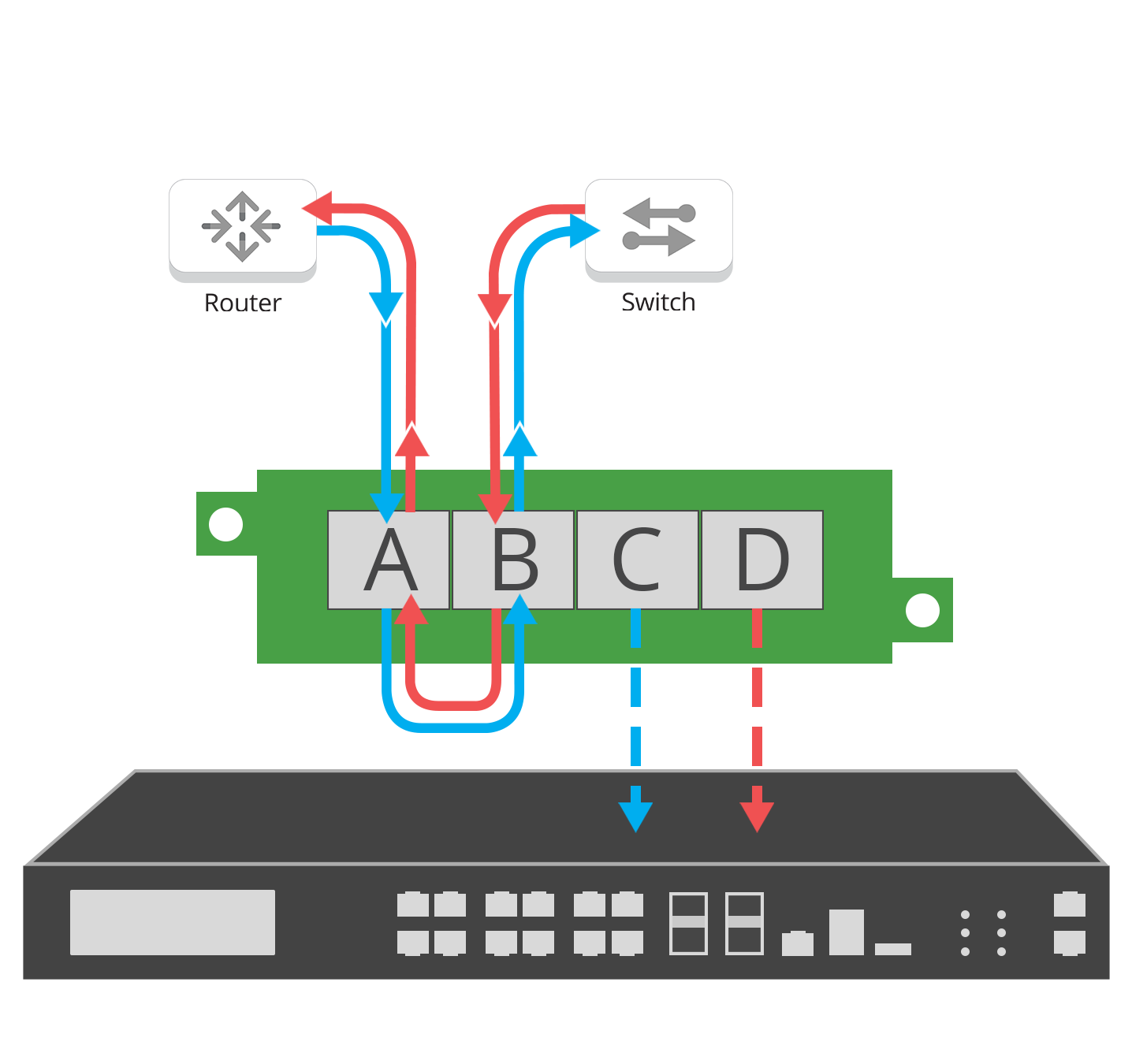
Monitoring and security tools need complete packet data to properly analysis the task at hand. If a threat is missed because of incomplete data or latency is introduced into the network, the solution has failed. Your options to provide these packets are spanning a port from your switch or utilizing a network TAP.
Dropped packets or packet loss can occur when packets of data traveling across a network fails to reach their destination. Packet loss is can be caused by network congestion, hardware capacity and bottlenecks, errors in data transmission, or overloaded devices.
Packet loss is measured as a percentage of packets lost compared to packets sent. The Transmission Control Protocol (TCP) is the standard that defines how to establish and maintain a network conversation through which application programs can exchange data. TCP detects packet loss and performs retransmissions to ensure reliable messaging. Monitoring packet loss is a fundamental best practice for network performance.
Network congestion, hardware capacity, bottlenecks and overloaded devices can all be symptoms of an over reliance on SPAN ports for network monitoring. SPAN is commonly known to drop packets if a port is oversubscribed. The issue arises when the total amount of traffic aggregated from the source ports exceeds the physical limitations of the destination port, it results in some dropped packets on the destination port.
This does not cause any switch performance degradation or disruption or traffic flow on the source ports. The only affected port is the destination port, and it drops packets on a first in first out (FIFO) basis once the egress buffer limit is exceeded.
• Monitoring tools may miss packets due to SPAN port over-subscription
• SPAN will not pass corrupt packets or errors (bad packets) and are dropped
Solution
Network TAPs ensure no Packet Loss
Network TAPs ensure no dropped packets or packet loss, by providing full-duplex copies of packet data, providing a complete picture for monitoring and security tools to analyze network traffic.
• Purpose-built to pass 100% full duplex traffic
• 100% network visibility
• Pass every packet, including physical layer errors
• Support jumbo frames.