Together, ExtraHop and Garland Technology eliminate blind spots in an IT network.
Click to learn more
Garland Technology’s network TAPs and packet brokers aggregate the live wire for 100% packet capture in a network. In order to secure the data at the physical layer through these reliable network TAPs, the ExtraHop Reveal(x) platform provides real-time application visibility to monitor, protect, block, and analyze traffic in real-time, all the time.
ExtraHop makes data-driven IT a reality with real-time analytics and machine learning, turning the network into the most accurate and timely source of operational and security intelligence for everyone from the network engineer to the CIO. Cloud-native network detection and response (NDR) from ExtraHop Reveal(x) provides complete east-west visibility, real-time threat detection, and intelligent response capabilities through network traffic analysis (NTA) at scale.
Click to view benefits
Integration Benefits
ExtraHop Reveal(X) network detection and response for the enterprise works with Garland to help SecOps teams detect, investigate, and respond to threats in just a few clicks for IT operations. Security Ops teams gain fast, accurate answers about the security performance for the hybrid enterprise.
Benefits for IT and Security Operations Teams
• Reliable zero-loss packet processing.
• Filter duplicated packets optimizing resource consumption, throughput, and storage capacity.
• Detect hidden threats with line-rate decryption processing.
• Full visibility across on-premise data centers and private, public (AWS, Azure, Google), or multi-cloud environments.
• Ensure no dropped packets and complete network visibility by passing all live wire data.
• Gain full control over traffic behavior with advanced traffic aggregation, load balancing, and filtering.
- How It Works
- Full PDF Solution Brief
- Bundle start-up Guide
- Blog
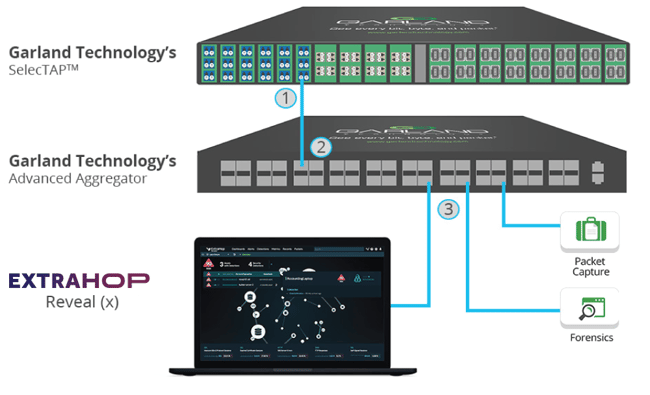
1. Garland’s high density passive SelectTAPTM provides 100% packet capture, allowing multiple tapped links to flow from the TAPs to Garland’s PacketMAXTM Advanced Aggregator.
2. The PacketMAX then aggregates, load balance, filter, and distribute the tapped traffic.
3. The aggregated traffic enters the ExtraHop Reveal(x) stream processor, which performs out-of-band decryption at line rate, protocol decoding, and full-stream reassembly at up to 100Gbps of throughput.
TAP -> TOOL
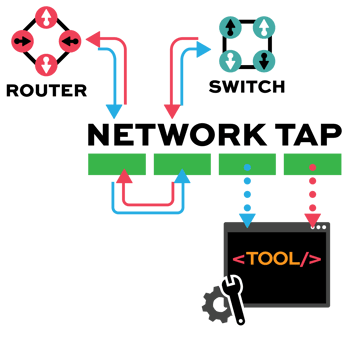
Network TAP Benefits
- Provide complete packet visibility with full-duplex copies of network traffic.
- Ensure no dropped packets while passing physical errors and support jumbo frames without delay or altering the data.
- Support speeds from 10/100M, 1G, 10G, 40G, 100G, and 400G are available in single-mode and multi-mode fiber or copper ethernet.
- Available in Tap ‘Breakout,’ aggregation, regeneration, bypass, and advanced filtering.
- Passive or failsafe – Does not affect the network.
- No IP address or MAC address, and cannot be hacked.







