Partners
Thank you for contacting us!
We appreciate your interest in network visibility. We will contact you immediately regarding your request.
If it is urgent, please call us at 716.242.8500.
In the meantime, browse the TAP Into Technology Blog below for industry news and best practices for network management and design.

The 101 Series: Filtering TAPs
| April 29, 2026
In our 101 network TAP series, we have explained the functionality of the various network TAPs that are available to gain access to the traffic that..
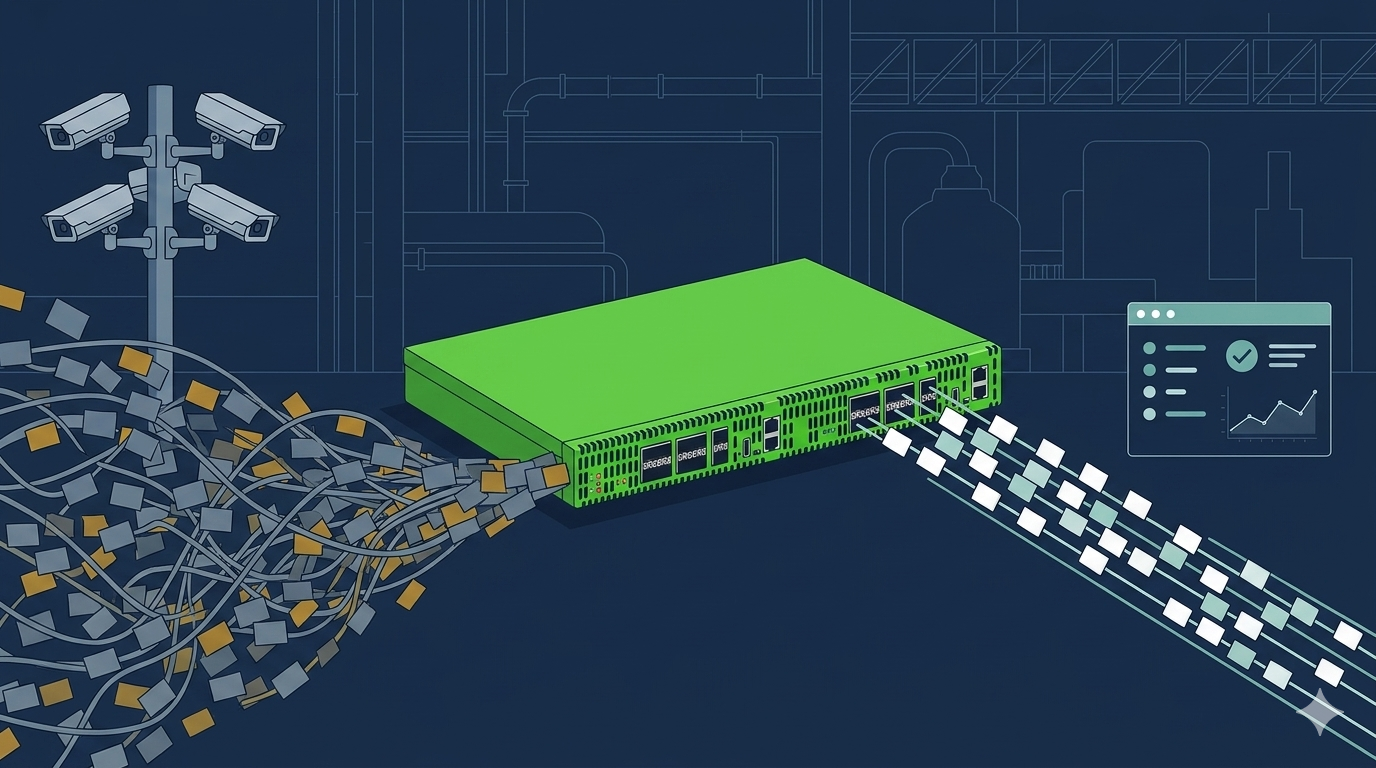
Precision Visibility: How Packet Filtering Transforms OT Monitoring
| April 16, 2026
How excessive video traffic from IP security cameras can overwhelm OT monitoring sensors and inflate IDS licensing costs. Why most OT teams don’t..

Renew Your Existing Packet Broker Without Increasing Fees
| April 2, 2026
Introduction Many organizations are being forced to extend the life of existing security and monitoring tools while budgets tighten and network..
