Discover how Garland Technology and Stellar Cyber are revolutionizing OT security! In this exclusive interview, Snehal Contractor, SVP of Worldwide Systems Engineering at Stellar Cyber, reveals how their Open XDR platform integrates with Garland's network TAPs and network packet brokers to provide unparalleled visibility and threat detection in OT environments.
Key points:
- 300+ OT-specific threat detections
- Machine learning for anomaly detection
- Graph-based correlation of OT and IT security events
- Unified visibility across OT and IT in a single interface
Stellar Cyber and Garland Technology partner to deliver a joint technical solution that allows enterprises to realize the right OT security program, regardless of data sources or network requirements, and remove that legacy challenge.
Stellar Cyber Open XDR Platform
- Ingests, normalizes, and enriches all your security data, including OT, endpoints, network, cloud, and logs into a single repository, replacing legacy SIEMs
- Automatically detects and correlates alerts using a proprietary multi-modal threat detection engine driven by machine learning
- Reduce attacker dwell time, minimizing attack impact
- Collects and detects in edge environments, including OT, with multi-function network security sensors
- Provides automated and manual response actions in real-time
Garland Technology Network Visibility Solution
- Provides 100% complete network visibility through Network TAPs (Test Access Points) without affecting network traffic
- Optimize network monitoring through purpose-built Packet Brokers that allow advanced aggregation, filtering, load balancing, and deduplication
- Delivers inline Bypass TAPs to manage new inline tool deployments without disrupting operations
- Utilizes Data Diodes to segment network environments with unidirectional constraints
- Deployable solutions in specialized environments (e.g. OT) and in any form factor (hardware vs. virtual)
Stellar Cyber Solution Benefits
- Enhanced visibility reduces the risk of damaging breach
- Dramatic increase in security analysts' productivity and efficiency
- Reduce attacker dwell time, minimizing attack impact
- Improve ROI of your existing security stack investment in IT and OT
Garland Technology Solution Benefits
- Complete visibility regardless of the network architecture constraints
- Future proofed network monitoring to scale up to any speeds or changes in underlying infrastructure
- Reduce overall cost of network monitoring through complete portfolio of TAP and Packet Broker products
- Zero hardware subscription fees
Joint Approach To Defending OT
Stellar Cyber's role in defending OT environments is to get telemetry from every relevant system, deploy its sensors for NDR and other network-based detections in relevant environments, and perform automated threat detection to power the security operations program. Garland Technology's role in defending OT environments is to provide packet-level visibility, no matter the network architecture constraints, and provide unidirectional network segmentation.
The objective of deploying Stellar Cyber and Garland Technology is to get complete, cost-effective visibility which will ultimately deliver the best security outcomes. Both companies offer flexibility on specific products or components deployed depending on the deployment scenario. Use the below deployment matrix to understand how to deploy to defend your OT environment optimally. The deployment scenarios below reference the Purdue Model for Industrial Control Systems.
| Deployment Scenario |
Stellar Cyber Architecture |
Garland Technology Architecture |
| 1. Agentless network Security Sensors allowed in Level 3 and Level 2 | • Security Sensors deployed in Level 3 and Level 2 off of core switches • OT syslog collected directly to Security Sensors |
• TAPs optional depending on physical network requirements (media type/speed) |
| 2. Agentless network Security Sensors NOT allowed in Level 3 and Level 2 | • Security Sensors deployed in Level 4 off of packet broker • OT syslog collected via syslog server sending telemetry to Level 4 |
• Packet Broker deployed in Level 3 • Aggregator TAPs deployed in Level 2 sending traffic to Packet Broker • Data Diode optional depending on unidirectional requirements |
| 3. Require unidirectional connectivity between Level 4 and Level 3 environments | • Security sensors in Level 3 and below must be manually updated | • Data Diode deployed between Level 3 and Level 4 |
| 4. Legacy or unmanaged switches | • Security Sensors deployed in Level 3 and Level 2 off of Network TAPs, if allowed • Otherwise, Network TAPs feed Packet Broker, which then feeds Security Sensors |
• Network TAPs deployed to mirror switch traffic to Security Sensors |
| 5. DMZ hosts allow agents for security | • Agent Sensors deployed on DMZ hosts for telemetry collection | Does not affect architecture |

Stellar Cyber Open XDR platform delivers comprehensive, unified security without complexity, empowering lean security teams of any skill to successfully secure their environments. With Stellar Cyber, organizations reduce risk with early and precise identification and remediation of threats while slashing costs, retaining investments in existing tools, and improving analyst productivity, delivering a 20X improvement in MTTD and an 8X improvement in MTTR. The company is based in Silicon Valley. For more information, contact stellarcyber.ai
Stellar Cyber and Garland Technology partner to deliver a joint technical solution that allows enterprises to realize the right OT security program, regardless of data sources or network requirements, and remove that legacy challenge.
Stellar Cyber Open XDR Platform
• Ingests, normalizes, and enriches all your security data, including OT, endpoints, network, cloud, and logs into a single repository, replacing legacy SIEMs
• Automatically detects and correlates alerts using a proprietary multi-modal threat detection engine driven by machine learning
• Reduce attacker dwell time, minimizing attack impact
• Collects and detects in edge environments, including OT, with multi-function network security sensors
• Provides automated and manual response actions in real-time
Network Visibility Solution
Garland Technology
• Provides 100% complete network visibility through Network TAPs (Test Access Points) without affecting network traffic
• Optimize network monitoring through purpose-built Packet Brokers that allow advanced aggregation, filtering, load balancing, and deduplication
• Delivers inline Bypass TAPs to manage new inline tool deployments without disrupting operations
• Utilizes Data Diodes to segment network environments with unidirectional constraints
• Deployable solutions in specialized environments (e.g. OT) and in any form factor (hardware vs. virtual)
Solution Benefits
Stellar Cyber
• Enhanced visibility reduces the risk of damaging breach
• Dramatic increase in security analysts’ productivity and efficiency
• Reduce attacker dwell time, minimizing attack impact
• Improve ROI of your existing security stack investment in IT and OT
Garland Technology
• Complete visibility regardless of the network architecture constraints
• Future proofed network monitoring to scale up to any speeds or changes in underlying infrastructure
• Reduce overall cost of network monitoring through complete portfolio of TAP and Packet Broker products
• Zero hardware subscription fees
TAP -> TOOL
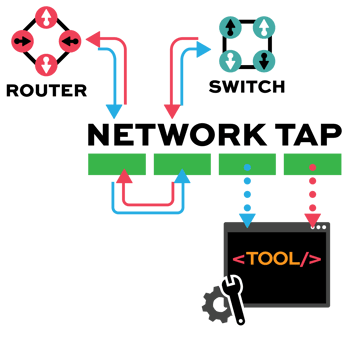
Network TAP Benefits
- Provide complete packet visibility with full-duplex copies of network traffic.
- Ensure no dropped packets while passing physical errors and support jumbo frames without delay or altering the data.
- Support speeds from 10/100M, 1G, 10G, 40G, 100G, and 400G are available in single-mode and multi-mode fiber or copper ethernet.
- Available in Tap ‘Breakout,’ aggregation, regeneration, bypass, and advanced filtering.
- Passive or failsafe – Does not affect the network.
- No IP address or MAC address, and cannot be hacked.
- Full PDF Solution Brief
- Joint Approach To Defending OT
Stellar Cyber’s role in defending OT environments is to get telemetry from every relevant system, deploy its sensors for NDR and other network-based detections in relevant environments, and perform automated threat detection to power the security operations program. Garland Technology’s role in defending OT environments is to provide packet-level visibility, no matter the network architecture constraints, and provide unidirectional network segmentation.
The objective of deploying Stellar Cyber and Garland Technology is to get complete, cost-effective visibility which will ultimately deliver the best security outcomes. Both companies offer flexibility on specific products or components deployed depending on the deployment scenario. Use the below deployment matrix to understand how to deploy to defend your OT environment optimally. The deployment scenarios below reference the Purdue Model for Industrial Control Systems.
| Deployment Scenario |
Stellar Cyber Architecture |
Garland Technology Architecture |
| 1. Agentless network Security Sensors allowed in Level 3 and Level 2 | • Security Sensors deployed in Level 3 and Level 2 off of core switches • OT syslog collected directly to Security Sensors |
• TAPs optional depending on physical network requirements (media type/speed) |
| 2. Agentless network Security Sensors NOT allowed in Level 3 and Level 2 | • Security Sensors deployed in Level 4 off of packet broker • OT syslog collected via syslog server sending telemetry to Level 4 |
• Packet Broker deployed in Level 3 • Aggregator TAPs deployed in Level 2 sending traffic to Packet Broker • Data Diode optional depending on unidirectional requirements |
| 3. Require unidirectional connectivity between Level 4 and Level 3 environments | • Security sensors in Level 3 and below must be manually updated | • Data Diode deployed between Level 3 and Level 4 |
| 4. Legacy or unmanaged switches | • Security Sensors deployed in Level 3 and Level 2 off of Network TAPs, if allowed • Otherwise, Network TAPs feed Packet Broker, which then feeds Security Sensors |
• Network TAPs deployed to mirror switch traffic to Security Sensors |
| 5. DMZ hosts allow agents for security | • Agent Sensors deployed on DMZ hosts for telemetry collection | Does not affect architecture |