

The aggregation layer, and thus the four-tiered approach to network visibility grew out of the need to maximize the ROI of NPBs and monitoring and security tools. Before we talk about the aggregation layer and the benefits it brings, let’s take a step back to see how we got here.
Networks began with simply connecting a monitoring tool directly to the SPAN port on the switch. Bandwidth was so low, that if a tool had to be updated or inspected, there was no concern with unplugging the device. However over time, as networking demands grew, there was no way that networking teams could essentially unplug their networks every time they wanted to configure or update monitoring tools. Thus the rise of network TAPs to provide dedicated access to all of the packet level traffic at a point in the network. And soon after came network packet brokers, combining multiple traffic streams and other advanced functionality, before feeding that traffic to your monitoring or security tool of choice. Thus the 3 tier approach to network visibility.
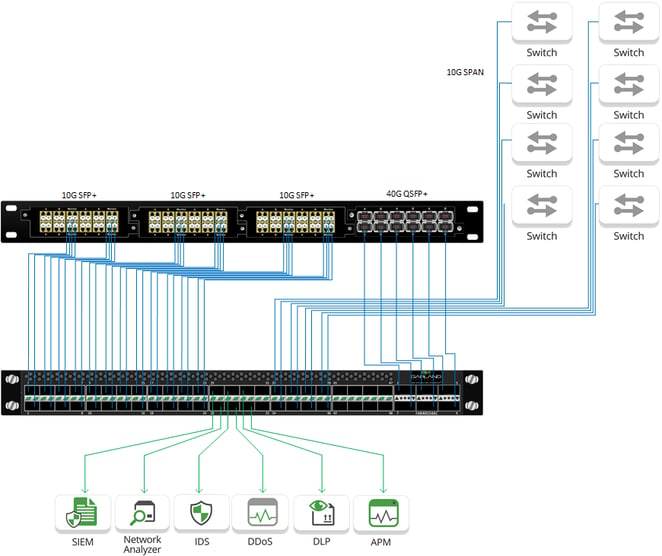
In the traditional three-tiered approach an assortment of tools are used for application performance monitoring, security, data forensics, and more. The only problem is that the tools continue to represent the most expensive aspect of network monitoring due to increasingly higher speeds and advanced features. To support these tools, network architects have had to deploy more complex NPBs, which has only added to the costs of overall network design and diminished long-term ROI.
.png?width=662&name=Aggregation%20to%20NPB%20(transparent).png)
The reality of today’s large networks is that many links only use less than 60% utilization, and in distributed networks as you move further from the data center core, link utilization can often drop below 5%. Add this low utilization to the fact that per port costs of network packet brokers are so high, network architects are left with minimal ROI. But by adding an aggregation layer to the traditional three-tiered network, the issues around ROI are solved.
The difference made by the addition of an aggregation layer is significant. Consider this simple example. If an existing network packet broker has 50% utilization on all of the ports, adding in an aggregator has the potential to free up half of the ports on the NPB, by aggregating 2 links into one port on the NPB. Multiply that exponentially, and the value is obvious. Aggregation extends the timeline for purchasing additional NPBs, while also allowing network admins to monitor parts of the network that previously had been considered blind spots.
When making the decision to add in an aggregation layer to maximize ROI, network architects should look for devices where costs do not exceed $1,000 per 100G interface. This per port cost is anywhere from 50-75% less than a full-featured network packet brokers that would be under-utilized in most scenarios. Additionally, network architects should look for an aggregator that is capable of supporting multiple speeds and media types, creating more flexibility in meeting network needs. Aggregators should also be capable of selective Layer 2 through Layer 4 pre-filtering to further reduce traffic before it is sent out to the NPB, integrate with management software through APIs, and have remote management options.
Choosing the right aggregators isn’t just about cost efficiency. Strategically deploying the right devices can help you add additional value to your network visibility layer and the IT organization as a whole.
Looking to add aggregation to your next deployment, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do!
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.