
January 9, 2020

When you’re driving on a foggy day, how can you stay safe when you can’t even see the road in front of you? Blind spots in the car are similar to blind spots within your cloud-based data center if not properly monitored.
Securing your network and keeping data integrity in the cloud can equate to millions of dollars lost in operational and downtime costs, if not done properly. It’s imperative to weather the storm and be prepared for your organization’s cloud migration to deliver sufficiently detailed network insight.
Most operations can’t forge a comprehensive overview of their user experience. This helps to instantly distinguish between problems that arise in the network as opposed to the application. In today’s economy performance equates to dollars, so having business-critical applications are expected to perform at a consistent quality.
With cloud being the future of networking, transitioning resources from traditional on-prem data centers to public, private, hybrid, or multi-cloud environments, opens your network to blind spots and malicious activity, making planning for the future difficult. Flowmon and Garland Technology mitigate those challenges by providing packet-level visibility and monitoring of your network.
As the nervous system of every modern organization, service delays diminish customer experience and satisfaction. These degradations can cost millions of dollars for you as they interfere with the fulfillment of business goals and can even harm reputation. That is why businesses need visibility into network traffic if they wish to respond before they suffer financial consequences.
By providing mirrored data traffic to the Flowmon tools both in the cloud and on-premise, this solution creates instant insights, where traditional layer 2 tapping may not be effective. This information is necessary to resolve network performance issues, identify opportunities to optimize, and ensure the entire infrastructure across the different environments supports business-critical services.
Garland Prisms filters and distributes cloud packet traffic to the Flowmon Collector equipped with a built-in probe for flow generation. Flowmon’s DPI engine improves traditional flow to bring immediate noiseless insight, reporting, and analytics on specific application protocols. Flowmon and Garland Technology provide a complete visibility solution into your cloud-based environments. By turning your cloud infrastructure into a transparent environment, the solution provides powerful analytics with AI-powered incident detection to enable effective monitoring for superior user experience.
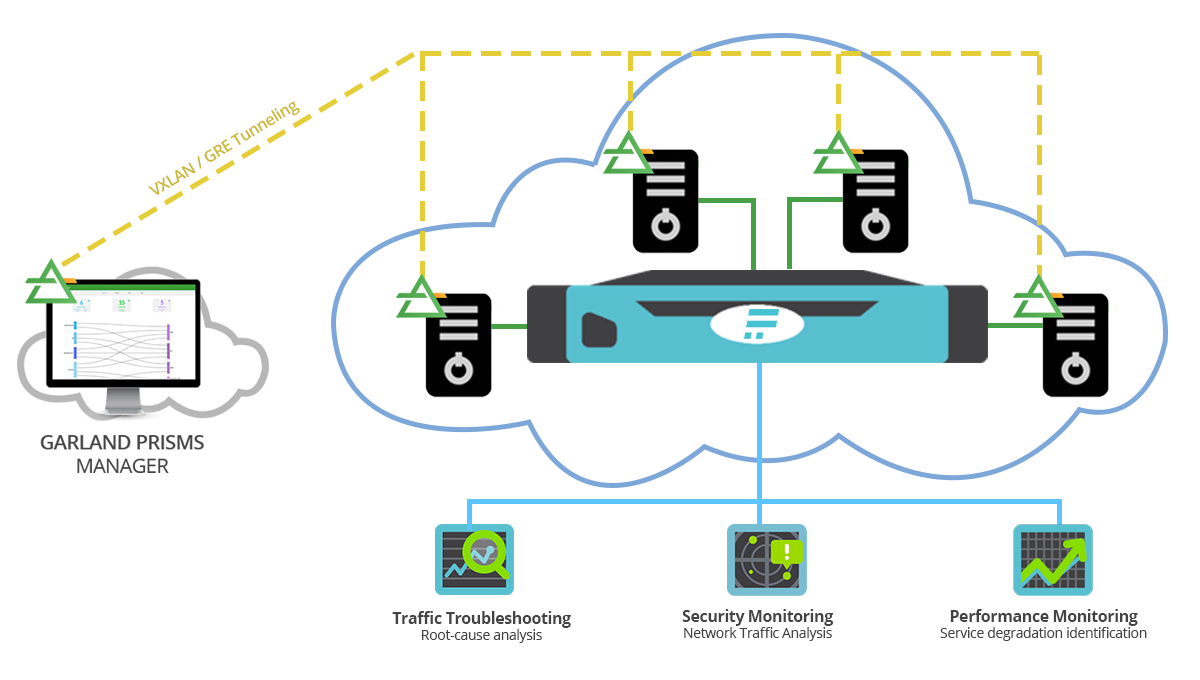
The configuration of Garland Prisms and Flowmon is simple - The combination of the two solutions results in crystal-clear visibility into cloud/hybrid infrastructure, enabling immediate and deliberate incident response. Setting the destination IP for mirrored traffic and decapsulation method on the Flowmon Collector. You can optimize performance, detect insider threats or leverage hard data to hold service providers accountable for degradations. Significant incidents are recorded for effective and detailed post-compromise analysis so that you are never in the dark when it comes to keeping your system safe and functioning.
Getting in-depth visibility into your cloud environment, whether public or private is difficult. When migrating your business operation to the cloud, Flowmon and Garland give you clear vision is not only critical for understanding activity but is also vital for maintaining a good customer experience.
[Interested in learning more? Book a demo of Prisms with a member of our Solutions Engineering team or get started with your free trial today!]
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.