Our infrastructure is at risk. In 2013, an Iranian hacker broke into the flow control mechanism for a dam in upstate New York. Only the fact that the dam itself was broken prevented him from remotely controlling the structure.
In Ukraine, a variant of the BlackEnergy virus was used to shut down part of the country's power grid.
The message is clear—hackers are increasingly turning their attention towards the everyday miracles that provide us with water and electricity, and those systems are wide open.
Industrial Control Systems and Supervisory Control and Data Acquistion (ICS/SCADA) devices monitor and control our heavy-duty infrastructure, but these systems came into vogue long before the dangers of hacking were well-understood. None of these systems were designed from the ground up to interface with security architecture. Most ICS/SCADA systems are protected only by a firewall, and network operators have little moment-to-moment understanding of who or what may be trying to interface with them. By the time administrators get around to looking at their logs, attackers may have been and gone.
What's so Smart About Passive Real Time Monitoring?
As stated, most ICS/SCADA systems are protected by firewalls. These firewalls don't just serve the purpose of hiding the system's control interface from people who just happen to be browsing the internet—as was the case with the New York dam mentioned above. They also segment the ICS/SCADA from business networks, meaning that you can't hack into an office and move laterally to control utilities and manufacturing equipment.![]() The problem is that firewalls are generally the only thing protecting ICS/SCADA systems. They tend not to even have authentication controls—you don't need a username or password to start messing around with them. Thus, any attacker who gets past the right firewall will basically own your ICS/SCADA by
The problem is that firewalls are generally the only thing protecting ICS/SCADA systems. They tend not to even have authentication controls—you don't need a username or password to start messing around with them. Thus, any attacker who gets past the right firewall will basically own your ICS/SCADA by
default.
>> Download now: Learn how to secure your industrial network
[Free Whitepaper]
Once your ICS/SCADA system is breached, there's no limit to the damage that an attacker can cause. Forget deliberate sabotage for now. Prior to its use in disrupting the Ukrainian power grid, the BlackEnergy malware was mostly used for industrial espionage. Imagine an attacker with the ability to derive your trade secrets by invisibly spying on your manufacturing process, and you'll understand one of the primary dangers that stem from this sort of attack.![]() Putting the focus back on monitoring is important. The ability to observe, in real time, any changes that occur in ICS/SCADA means more than just protection from hackers. When these systems deviate from the baseline, it can indicate out-of-control processes, equipment malfunction, or even cause industrial accidents. Having a pair of eyeballs on these systems at all times mean that network operators can identify and remediate any unanticipated changes in ICS/SCADA systems, before anyone gets hurt.
Putting the focus back on monitoring is important. The ability to observe, in real time, any changes that occur in ICS/SCADA means more than just protection from hackers. When these systems deviate from the baseline, it can indicate out-of-control processes, equipment malfunction, or even cause industrial accidents. Having a pair of eyeballs on these systems at all times mean that network operators can identify and remediate any unanticipated changes in ICS/SCADA systems, before anyone gets hurt.
How is Passive Real Time Monitoring Accomplished?
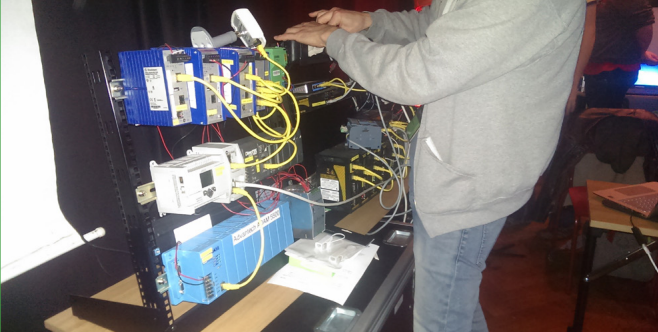
 As far as ICS/SCADA systems are concerned, the ability to see every bit, byte and packet® couldn't be more crucial. Garland Technology offers a network aggregating TAP that can capture 100 percent of duplex network traffic and send it along to your choice of monitoring solution. As many industrial solutions are still copper-based, we recommend our PT100 TAPs in 10/100M copper with Aggregation.
As far as ICS/SCADA systems are concerned, the ability to see every bit, byte and packet® couldn't be more crucial. Garland Technology offers a network aggregating TAP that can capture 100 percent of duplex network traffic and send it along to your choice of monitoring solution. As many industrial solutions are still copper-based, we recommend our PT100 TAPs in 10/100M copper with Aggregation.
Understanding how to correctly monitor ICS/SCADA systems is crucial to security on a number of different levels. When utilities are affected by malicious attackers, it affects national security. When attackers can harness compromised ICS/SCADA systems to steal IP, financial security is affected. When unmonitored systems begin to malfunction, the personal safety of your workforce is at risk. Only by carefully monitoring these industrial control systems can a greater measure of safety be achieved.
Looking to add a visibility solution to your industrial deployment, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do.