

With enterprises moving core business functions to the cloud, network security teams have an even bigger challenge ahead of them to properly protect their networks without sacrificing accuracy or the time it takes to detect and respond to threats to both the physical and cloud environments.
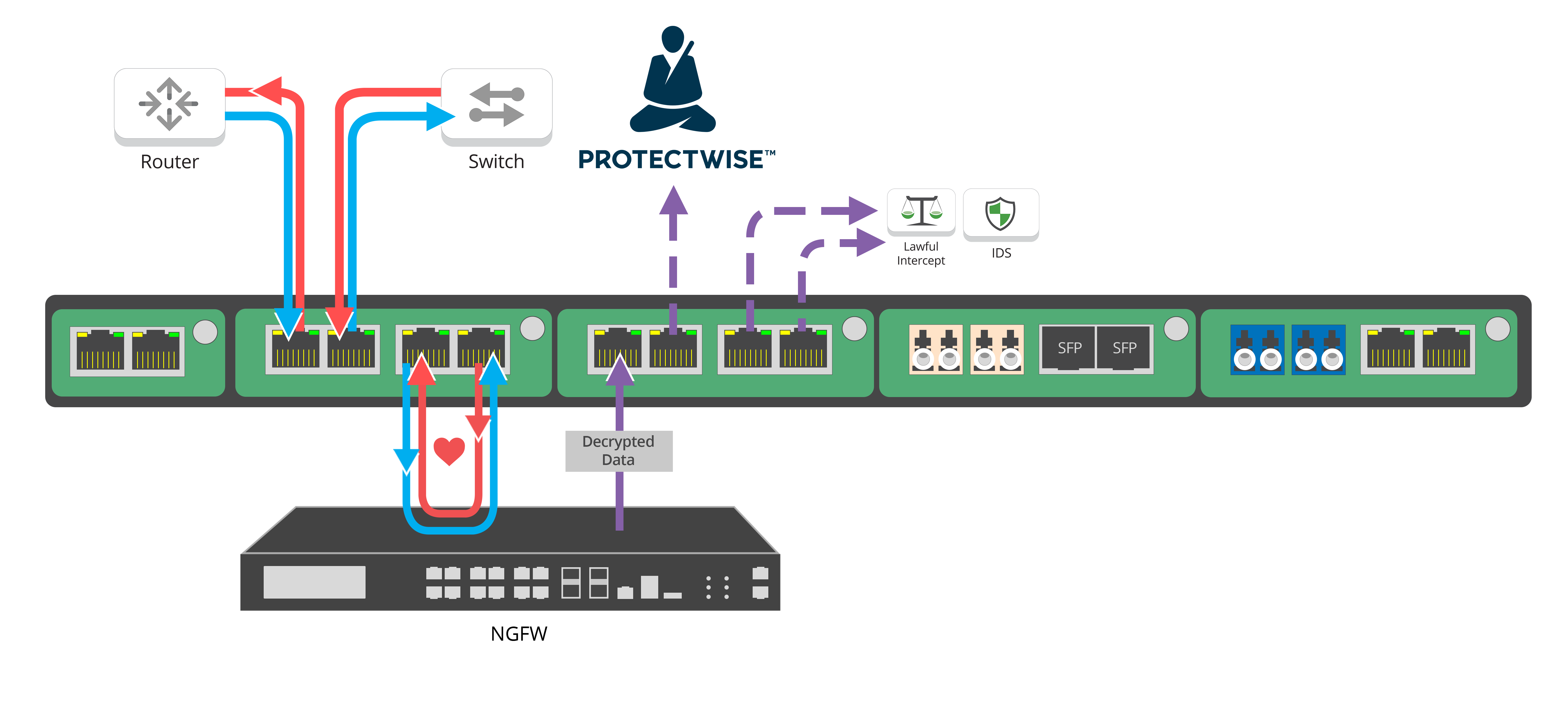
The Garland and ProtectWise solution provides 100% network visibility with an end-to-end infrastructure that eliminates blind spots in your network. With Garland Network TAPs tapping the wire and ensuring 100% packet capture, The ProtectWise Grid™ is capable of providing automated network detection and response all in one single interface. The solution offers:

Visibility is essential to The ProtectWise Grid, which creates a lasting, high-fidelity memory of activity on the network, by capturing and storing traffic into a single destination in the cloud. This gives you the ability to know whether threats have ever jeopardized your network. Without 100% visibility, The ProtectWise Grid would be unable to guarantee that the historical data being presented and analyzed is accurate.
Garland Technology's Network TAPs and purpose built packet brokers also provide the flexibility to make policy changes based on real-time data, determine baseline traffic and eliminate the risk of oversubscribed SPAN ports.
Why does ProtectWise partner with Garland Technology? The answer's simple. We deliver 100% packet capture, test and validate every Network TAP with live data, and have scalable solutions for networks up to 100G.
[Want to learn more about The ProtectWise and Garland Technology solution? Watch our on-demand webinar with ProtectWise to see how the solution works with the addition of a Palo Alto NGFW.]
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.