Network TAPs provide the best and easiest way to see network traffic going over the network. Simply plugging the tap into the physical cables between two networked devices will capture each packet sent across that wire. By strategically placing taps across key points in the network, administrators gain full network visibility.
But what happens inside of a virtual environment?
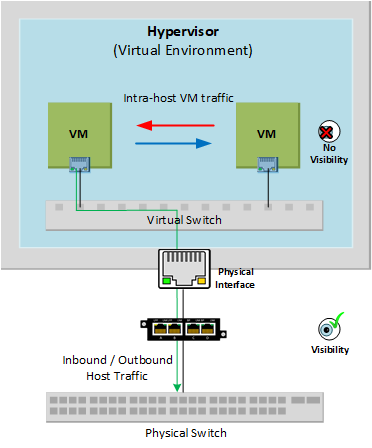
Traffic between virtual machines inside of a host never have to leave the host. Since this traffic doesn’t travel across a physical network connection, it won’t be captured by a Network TAP. The TAP will only catch traffic that connects a virtual machine to a resource outside the host. This creates a visibility blackhole to all east-west traffic between virtual machines.
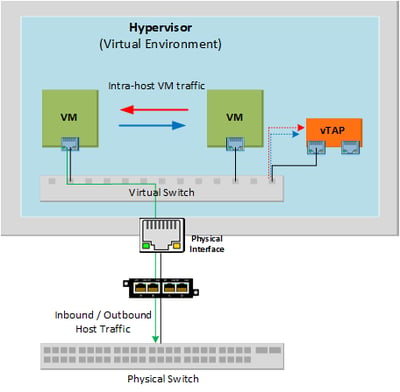
Visibility into a virtual network can be obtained with a Virtual TAP. Adding a virtual TAP into a host can capture the east-west communications between virtual machines.
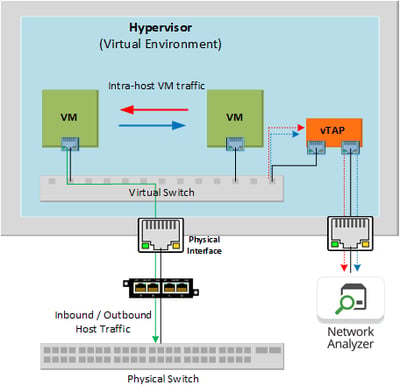
The virtual TAP can then direct this captured traffic out of a physical interface on the host, allowing the tapped virtual traffic to be sent to a physical tool.
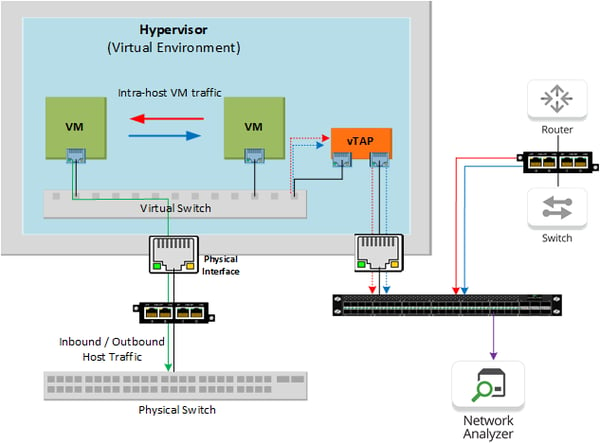
When sending the tapped traffic to aggregation appliance, both virtual traffic and monitor links from physically tapped cables can be combined. This combined traffic offers full visibility into the entire network that can be sent to both network and security monitoring tools.
[Want to learn more about the capabilities of Garland Technology's virtual TAP? Contact a member of our design team to learn how the vTAP can work within your virtual environment.]
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.