
Firewalls are the most recognized security tool for safeguarding your network and are a critical component of any security infrastructure. Firewalls are considered the gatekeeper for most network security architectures, allowing only defined traffic on the network.
Basically a firewall monitors incoming and outgoing network traffic, and based on a defined set of security rules the firewall decides whether to allow or block specific traffic. Firewalls establish a barrier, or “firewall,” between a trusted network and an untrusted network, typically on critical links like the Internet.
The main purpose of a firewall is to prevent attacks on a private network, allowing you to monitor the security of your network, when alerting suspicious activity occurs. The firewall also helps control the use of the Internet, blocking inappropriate or unblocking appropriate material, while monitoring services using WWW (World Wide Web), FTP (File Transfer Protocol), as well as other protocols.
Bottom line, the firewall prevents unauthorized access to your network, protecting your data from being compromised and is considered a bedrock of IT security stacks along with Intrusion Prevention System (IPS) and Security Information and Event Management (SIEM). Here we want to review which firewall you may need to deploy and best practices for managing availability of inline firewalls.
The Evolution of Network Firewalls
As digital threats have evolved, so have firewalls — leading to a range of added functions for specific needs. Business networks using firewalls to protect the broader network, have two basic categories — network-based or host-based firewalls.
Network-based firewalls are used strategically within a LAN or WAN. These are either a purpose-built hardware firewall appliance, a firewall software run within general-purpose hardware like a server, or virtual firewalls run off a virtual host hypervisor.
Host-based firewalls, deployed directly on the host itself, control network traffic within an operating system or an agent application for protection.
From network-based and host-based firewalls there are a growing number of network firewall evolutions that have emerged in the past 25 years, you may be familiar with:
1-Packet Filter Firewalls
Packet filtering firewalls inspect packets transferred between network segments where inline devices such as routers and switches connect and process data. This firewall maintains an access control list or established criteria that filters allowed IP addresses, packet type, destination ports and packet protocol headers. These criteria filters determine if the packets are forwarded, flagged or dropped.
Packet filtering firewalls are efficient at processing packets and are known for enabling complex security policies. These firewalls cannot filter at the application layer, can be complex to configure and are vulnerable to spoofing attacks.
2-Stateful Inspection Firewall
What is now considered the “traditional” firewall, a stateful inspection firewall tracks network operations and connections, allowing or blocking traffic based on state, port, and protocol. These firewalls examine each packet and keep track of whether or not they are part of an established TCP or other network sessions.
Stateful inspection firewalls have the capability to block attacks aimed at protocol gateway exploits and denial-of-service attacks (DDoS), can reduce the attack service, by operating with fewer open ports and tend to offer more security than either packet filtering. These firewalls tend to not be effective against stateless protocols and are known to affect network performance.
3-Application Firewall (proxy firewall)
An application-level firewall, also known as a proxy firewall or Web application firewall, is the gateway between one network application to another, built to control network traffic on any OSI layer up to the application layer. This firewall filters packets specified by the destination port or by other characteristics, like the HTTP request string.
Application layer filtering processes applications and protocols such as File Transfer Protocol (FTP), Domain Name System (DNS), or Hypertext Transfer Protocol (HTTP), allowing it to identify unwanted applications. Application layer gateways filters provide good data security and are used to obscure private network details, but can be complex to configure and can affect network performance with high processing overhead.
4-Next-generation Firewall (NGFW)
Next-generation firewalls are considered the next step in the evolution beyond packet filtering and stateful inspection, used to identify and block advanced malware and other dangerous attacks.
NGFWs combine standard stateful inspection firewall capabilities with intrusion detection/prevention, deep packet inspection and malware filtering providing advanced protection and are capable of monitoring network protocols from layer 2 through the application layer 7. Consolidation of disparate security functions are known to create a possible point of failure and are known to be complex and process intensive.
Other types of firewalls include, Circuit-level gateway firewalls, which are used to quickly identify malicious content, monitoring TCP handshakes and other network protocol sessions, and Unified threat management (UTM) firewall’s typically combine the functions of a stateful inspection firewall with intrusion prevention and antivirus.
>> Download Now: 3 Keys to Network Resiliency
[Free Whitepaper]
Firewall Best Practices for Avoiding Downtime
Firewall architecture is based on which type of firewalls you use, what links need to be protected — between specific servers, individual endpoints or at your network’s edge and how you plan to manage the availability. A deployment strategy for inline firewalls includes many configurations, protocols as well as failure and recovery scenarios. Deploying a tool inline comes with the inherent risk of creating network downtime. Here are 3 best practices for avoiding downtime with your firewall deployment.
1. Sandbox Deployment
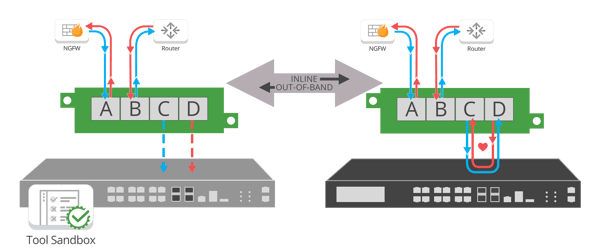
Firewalls are an inline appliance sitting between a network segment to look at all the traffic passing through that point. Deploying a firewall with an external bypass TAP allows you to sandbox in your real environment with live packet data, without impacting the availability of the network. This allows you to evaluate and optimize the firewall out-of-band, before deploying it live in your network. The firewall being tested is exposed to the same data it would be monitoring for a production deployment, rather than test data, increasing the confidence of the piloting being performed.
2. Inline Lifecycle Management
Today's firewalls have a multitude of advanced features and functions built-in to protect the network. With these additional features is the real potential for misconfigurations and missed maintenance. These issues lead to slow systems, blindspots and ultimately downtime.
Inline Lifecycle Management (ILM) is the strategy of managing your firewall’s availability — ultimately providing operational isolation by expedited problem resolution of unplanned downtime without impacting network connectivity. ILM allows you to easily take the firewall out-of-band for updates, installing patches, performing maintenance or troubleshooting to optimize and validate before pushing back inline.
3. Preparing for planned or unplanned downtime
As inline firewalls sit between network segments, managing the risk of downtime is a critical consideration when deploying these solutions. Downtime, whether planned or unplanned, can not only impact the functionality of the network but also impacts reputation and lost revenue to the company.
IT teams commonly face downtime:
- Deploying the firewall
- Oversubscribed devices, degrade network performance
- Misconfigurations and missed maintenance
- Device failures
External bypass TAPs provide three resilient technologies to combat unplanned network downtime for inline firewalls, network failsafe, heartbeat technology and remote management.
Failsafe ensures the bypass TAP itself, and by extension the firewall, doesn’t become a single point of failure. If the bypass TAP loses power or were to fail, fail-safe technology simply triggers the network ports to bypass the TAP and connected firewall keeping the network up, or automatically triggering a redundant High Availability (HA) solution.
Heartbeat packets monitor the health of the firewall. Instead of relying on the direct connectivity of the network to the tool, the bypass TAP is purpose-built, designed specifically to pass heartbeat packets back and forth to detect an issue with the connected appliance. If the heartbeat sent from the TAP is not received back, indicating the device is offline, the TAP will automatically bypass the firewall, keeping the network up even though the device is offline. No network downtime. No single point of failure.
Remote Management enables direct interaction with bypass TAPs to manage inline security device lifecycle. With API level access, remote management of inline devices can be automated and scaled across dozens/hundreds of remote locations. This enables NetOps teams to quickly patch and upgrade critical appliances while maintaining remote connectivity to all remote locations.
Planned downtime also impacts network operations. External bypass TAPs provide administrative isolation, leading to no or minimal maintenance windows. Utilizing an external Bypass TAP offers the unique ability to implement inline lifecycle management for updates, installing patches, performing maintenance or troubleshooting.
A Bypass TAP has quickly become the essential complement to any inline tool, especially firewalls. Looking to add a bypass solution to your firewall deployment, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do.

