

It goes without saying, but proper application monitoring is a critical component of sound network management. Let the following example show you:
Say you have two critical 10G links that you need to monitor with a few inline network tools. That sounds like a big problem because each inline appliance has the potential of introducing a point of failure. Then, there is also the problem of getting all the network traffic from each critical link to go to each individual inline appliance for processing.
Sounds like a scenario that could be difficult and expensive to implement. But it doesn’t have to be.
By using Advanced Aggregation, you can increase the efficiency and port utilization of your network!
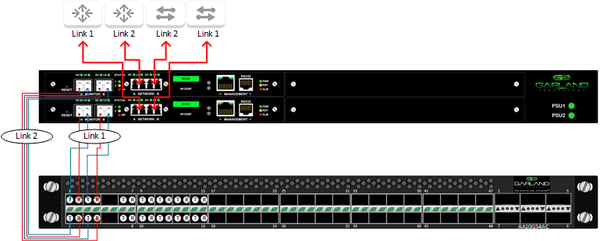
Bypass TAPs provide several benefits to your network when connected to inline appliances, but the most importantly, they eliminate the possibility that the inline appliance could create a point of failure for your network.

The Bypass TAPs cannot be connected directly to the inline appliance for two reasons. First because the network links are 10G and the appliances are 1G. And second, since you are trying to monitor two separate links, you would need two sets of monitoring tools to analyze the traffic.
By using the PacketMAX Advanced Aggregator, we can avoid these issues, since the Advanced Aggregator is purpose built to provide flexibility for your network. Each port on the Advanced Aggregators can be configured to receive inbound network traffic or to transmit outbound monitoring traffic. The Advanced Aggregator can also be set to load balance the traffic across the 5 appliances, so that the ports on the individual appliances are not oversubscribed. Finally, the Advanced Aggregators can tag the packets, so that when the packet is returned, it will know what link to return it to. This capability eliminates the second problem, removing the need for two sets of application monitoring appliances.
Connect your appliances to the Advanced Aggregator using the appropriate cables and pluggables.
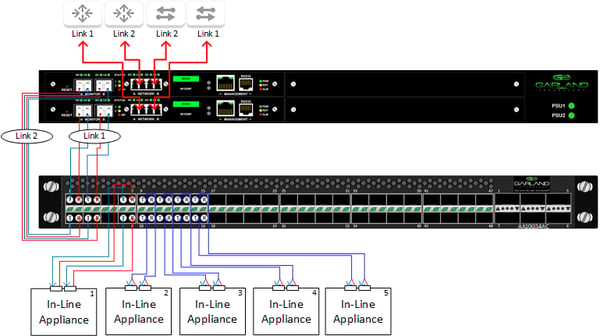
Program the Advanced Aggregator. It needs to be set up to load balance the traffic out to the monitoring appliances. Tag the packets so they can be returned to the proper link, and distribute the traffic out to the five 1G appliances. When the traffic is returned to the Advanced Aggregator after being processed by the application monitoring tools, it needs to remove the tags and return the packets to their proper 10G links.

Now that you’ve connected the inline appliances without introducing any points of failure, you are ready to analyze your traffic. You can even take your appliances offline, should you need to perform updates to the software or firmware, without scheduling a maintenance window of network downtime.
Looking to add an aggregation solution to your next deployment, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do!
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.