

We recently solidified a partnership with Napatech, a leading provider of solutions that achieve smarter data delivery to applications and ensure the quality and security of network services.
The pursuit of control over ever-increasing volumes (and speeds) of data across the network is something that resonates with us at Garland Technology.
But when you’re implementing a solution like the Napatech Pandion network recorder, it needs to be deployed in a way that ensures 100% visibility and real-time packet capture.
This is why we’ve partnered with Napatech—to ensure that the promise of real-time, on-demand access to packet-level data is fulfilled with the help of aggregator and optical network TAPs.
Here’s some more insight into what this partnership means for you.
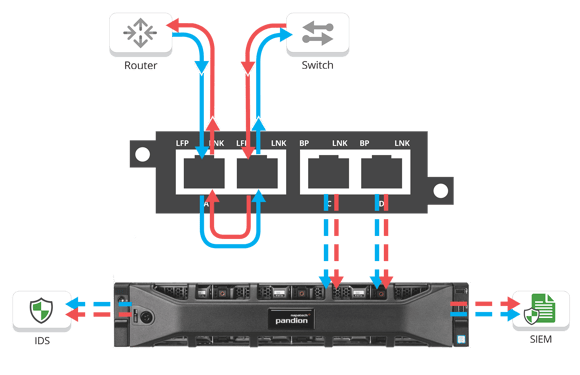 This diagram shows how our joint solution with Napatech works to provide 100% network visibility and guarantee complete real-time packet capture.
This diagram shows how our joint solution with Napatech works to provide 100% network visibility and guarantee complete real-time packet capture.
The network TAP is put in place to collect all traffic between a switch/router link. With aggregation and regeneration mode, the traffic can be copied to the ports connected to a solution like the Napatech Pandion.
With the help of network TAPs, Napatech Pandion can deliver on its promise to record 100% accurate full-packet captures and provide on-demand access to them in real-time.
When an IDS or DLP solution connected to Napatech Pandion generates an alert to SIEM dashboard, these on-demand full-packet captures allow analysts to dig deeper into the details and find root causes.
The partnership between Garland Technology network TAPs and Napatech Pandion result in end-user IT benefits such as:
[If you want to learn more about how network TAPs are helping Napatech (and how they can help you achieve your IT goals), check out our free white paper, Network TAPs 101: The Networking User Guide.]
There are so many innovative network monitoring and security solutions available to IT teams of all sizes today. But they all have one thing in common—the fact that incomplete packet visibility undermines performance.
While all IT teams face their own unique challenges, network visibility is a common challenge for everyone. The Napatech partnership showcases a use case for at least two types of network TAPs:
We’re happy to be partnering with Napatech to sustain the promise of 100% packet capture and visibility for enterprise and security provider applications. As we say at Garland Technology, network TAPs will always give you access to every bit, byte and packet®.
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.