
There are some great network tools on the market that provide protection for your organization's operations on the Internet. The problem with using them is that they can do the unthinkable by introducing a potential “point of failure” when inserted directly into the path of the Critical Link.
The Bypass TAP was developed specifically to resolve the problem of an inline security appliance causing a single point of failure.
How to Ensure Network Uptime in the Event of a Failure
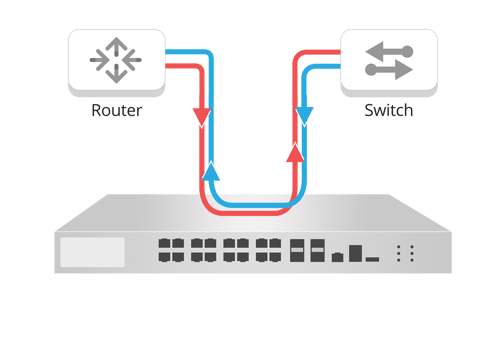
Inline of in-band security appliances, such as: Next-Gen Firewalls (NGFW), Intrusion Prevention System (IPS), Data Leakage Prevention (DLP), Web Application Firewalls (WAF), and Denial of Service (DDoS) are designed to protect your organization's network. But in order to do this, these appliances need to be placed into the path of the Critical Link. That way, if any problem occurs to cause the in band security appliance to go off-line, the critical link will stop flowing (see Figure 1 above). This is not a good thing for your Critical Links. Even if the in band security appliance only needs a software or firmware update, you would need to schedule downtime for your link.
The bypass TAP was developed specifically to resolve the problem of an in band security appliance introducing a “point of failure”. This TAP will keep the link flowing if the in band security appliance were to go off-line for any reason (Figure 2 below). It will also keep the link flowing even if the TAP were to lose power. This feature is commonly referred to as the 'failsafe.'
If the in band security appliance goes off-line, the TAP will bypass the appliance and automatically keep the link flowing. The bypass TAP does this by sending heartbeat packets to the in band security appliance and as long as the in band security appliance is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the in band security appliance.
Download Now: 3 Keys to Network Resiliency - A Security Engineer's Go-to Guide to Avoiding Network Downtime [Free whitepaper]
If the heartbeat packets are not returned to the TAP (indicating that the in band security appliance has gone off-line), the TAP will automatically 'bypass' the in band security appliance and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
Figure 3 (above) shows you the network traffic flow when the in band security appliance goes off-line (bypass mode). While the TAP is in bypass mode, it continues to send heartbeat packets out to the in band security appliance so that once the appliance is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the appliance is ready to go back to work. The TAP will then direct the network traffic back through the in band security appliance along with the heartbeat packets placing the appliance back in band.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our first blog on Network TAPs; if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Bypass TAPs in Passive Breakout 'aka Normal TAP' Mode
Another important feature to consider when deploying in band security network tools is, a Garland Technology bypass TAPs can be placed in the breakout, aggregation, or regeneration/SPAN mode. This provides lifelong value for the device, allowing you to repurpose it in your network as your demands change.
An added benefit of being able to set the bypass TAP in the breakout 'normal' mode is when you first deploy your in band security appliance. Breakout mode allows you to set everything - but in a passive mode so that you can sort out the possible false positive threat conditions before you actually place the in band security appliance in-line. Once you have figured that out, you can then set the equipment up for bypass mode for a nice, smooth transition for providing network safety for real threats without burdening the appliance with “false positive” threats. Our partners at Cloud Harmonics wrote a great blog on Best Practices for Deploying NGFW - the theory applies to any active, in band device.
The last feature I’d like to highlight with bypass TAPs is being able to analyze the critical link with other tools such as a WireShark analyzer or a Deep Capture Engine or other passive analysis tools. Alternatively, you may want to have a back up security appliance to take over should the primary appliance develop a problem or need to be updated.
Garland Technology's, The 101 Series is an educational series on how network TAPs work and the different functions they provide to the overall network design for access and visibility.
Looking to add a bypass solution to your security deployment, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do!

