
The factory of the future is digital and networked. The Industrial Internet of Things (IIoT) and Industry 4.0 are a further optimization of processes and faster production cycles for production companies and critical infrastructures. Industry 4.0 refers to the current trend of automation and data communication in manufacturing technologies. It includes cyber-physical systems, the Internet of Things, cloud computing and cognitive computing. The basic principle of Industry 4.0 is that by connecting machines, work pieces and systems; businesses are creating intelligent networks along the entire value chain that can control each other autonomously. In an Industry 4.0 factory, components and systems are able to gain self-awareness and become self-predictive, which will provide management with more insight on the status of the factory.
Industrial Control Systems (ICS) are the nervous system of highly efficient manufacturing in Industry 4.0. They are also characterized by increasing complexity and links to networks outside the industrial environment (i.e. the internet). The key to efficient and secure manufacturing is effective management of the ICS and the maintenance of high network quality. Only those who ensure digital transparency can protect their production against technical malfunctions, network failures, and advanced cyber threats.
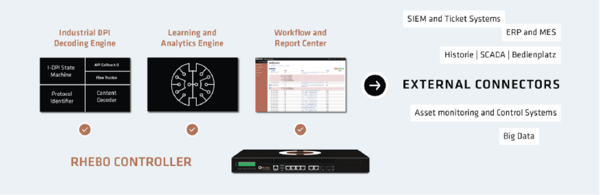
Rhebo Industrial Protector effectively controls, optimizes and protects complex ICS according to industry standards such as IEC 62443 and ISO 27001. Rhebo Industrial Protector monitors, analyzes and visualizes the complete data traffic in your ICS to the deepest content level. Individual commands between the components of the industrial control systems details are available and checked for changes. Rhebo Industrial Protector comprehensively detects and reports in real-time anomalies that could change or disrupt existing processes. As part of any defense-in-depth strategy, you gain 100% digital transparency and ability to react immediately to potential malfunctions before the supply processes are affected. Rhebo IIoT experts help networked industries to operate their control networks safely and without interference and to effectively implement their cyber security strategy.
>> Learn why SPAN Ports Should Not be used in Industrial Security Solutions
Rhebo + Garland Technology
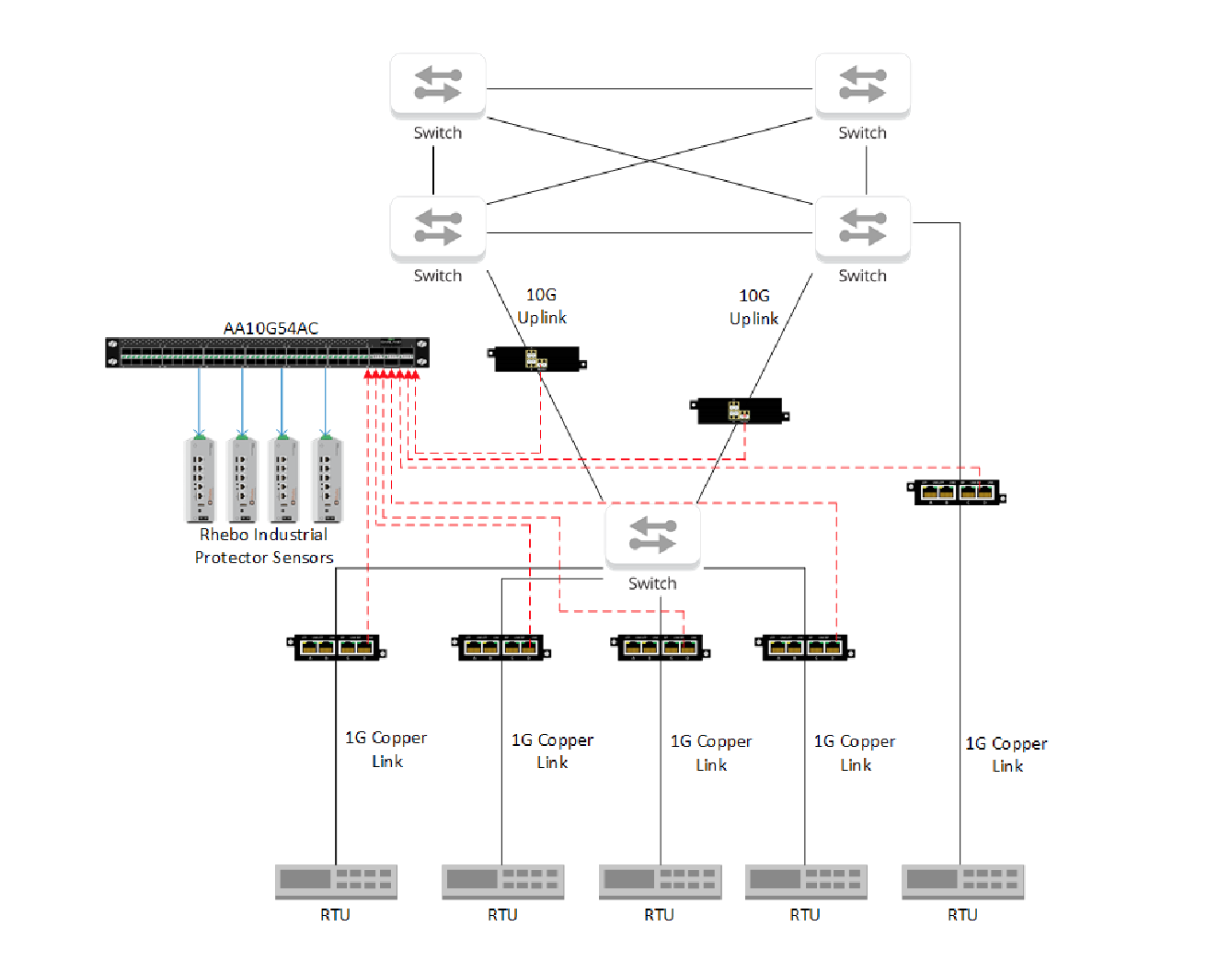
Rhebo Industrial Protector comprehensively and non-intrusively monitors the communication in process control and network control systems using Garland Technology TAPs. Any event that can lead to disruptions are detected and reported by the automatic anomaly detection. Such anomalies include both security incidents and technical malfunctions that occur in everyday tele-control operations. Ultimately, Rhebo Industrial Protector ensures plant availability, data integrity and thus long- term security of supply operations.
Several advantages are realized with the Rhebo and Garland Technology combined solution:
- Centralized monitoring of the network with listen-only aggregating TAPs
- Passive deployment in “monitor-only” mode but still allows for full anomaly detection and notification
- Minimal port consumption on centralized Rhebo Industrial Protector Controller or localized sensor devices
- 100% copy of network traffic without consuming additional ports on the network routing / switching infrastructure
- Reliable, very high MTBF solution
- Supports German power industry standards with 350,000 hours between TAP-point failure
- Quick resolution of any technical or supply issues by Garland Technology Support Services and local distribution partners
- Cost-efficient rack mount configuration with redundant power supplies
- Allows for installation of exact number of required TAPs plus cold redundancy TAP
- Combines four units in one RU or distributes TAP points through plant offering deployment flexibility
Multiple links and speeds can be aggregated, filtered and load balanced out to one or many Rhebo sensors simultaneously using Garland Technology’s Advanced Aggregator. The Advanced Aggregator can be used to reduce the total number of sensors required in the environment and to establish greater control and visibility over your monitored network.
Benefits for Operators of a Critical Infrastructure
Using Rhebo Industrial Protector will:
- Reduce cybersecurity risk and ensure security of supply through full network transparency and real-time anomaly detection.
- Ensure regulatory compliance with BDEW, ISMS, ISO/IEC 27000 and other standards using defense-in-depth and holistic infrastructure monitoring.
- With detailed audit trail and forensic data, achieve comprehensive incident reporting.
- Centralize monitoring of their network control technology via standard interfaces to SCADA, SIEM and other systems.
Using Garland Technology’s passive TAPs and Advanced Aggregators, operators can collect every bit, byte and packet necessary with Rhebo Industrial Collector. Garland Technology devices guarantee complete passive listening with no impact on the Industrial Control Systems (ICS) network processes.
- Garland Technology solutions support 1G, 10G, 40G and 100G network links.
- Garland Technology solutions support DIN Rail, a standardized industrial mounting system designed to reduce cost and time, while improving management.

