OT Segmentation Best Practices For a More Secure Industrial Network
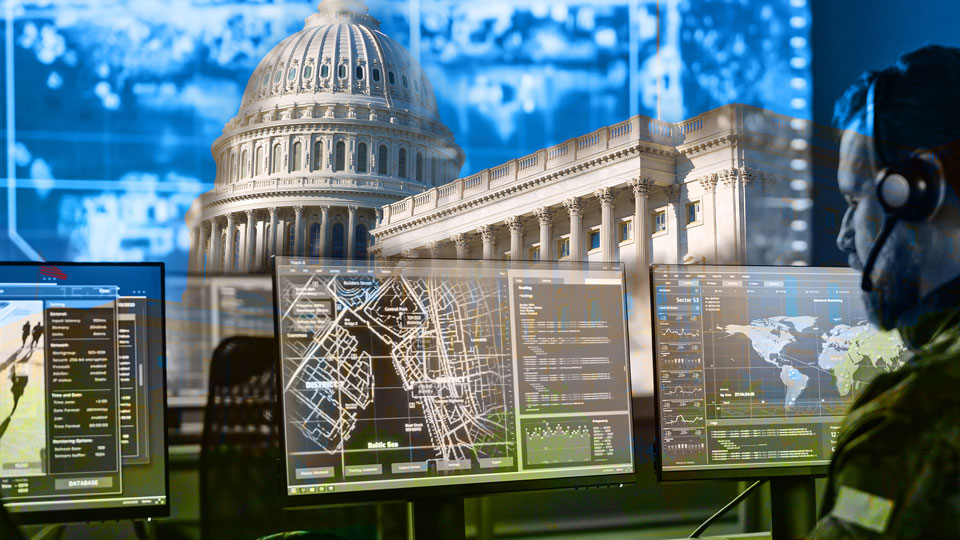
In the age of the Industrial 4.0 Revolution, data is king. It’s the impetus that drives IT/OT convergence in some of our most critical industries. Smart cities like Dallas are merging IP subnet-based...