
By moving workloads to a cloud IaaS (Infrastructure-as-a-Service) platform, you may think your infrastructure layers are completely outsourced, including the network side, and don’t need cloud performance monitoring.
You might also assume that since you’re not managing the network layer, you can keep using your current on-premise data center network visibility tools and don’t need to deploy a cloud traffic-specific monitoring solution.
There are specific reasons why you will need to have cloud traffic analysis capabilities. Some reasons are old. Some are new and have come with the ubiquitous presence that is the cloud.
Let’s start with the old ones, the reasons you had network monitoring in place within your traditional environment, which remain valid in the cloud:
- Performance troubleshooting: analyzing network traffic has always been a great source of performance analytics to understand end-user experience degradations and isolate the source of faults. This remains absolutely true in a cloud environment.
- Architecture decisions and optimization: there are always multiple ways to deploy infrastructure and applications, including in a cloud IaaS environment. Where will you locate resources across many regions and VPCs? These choices come with consequences in terms of complexity, economics, and impact on end-user experience. Cloud network forensics help you evaluate these options on the 3 dimensions and optimize your architecture.
- Security monitoring: security often starts with visibility and having a clear picture of who does what, where, and when. Cloud network forensics have a great advantage on other data sources both for threat detection and incident investigations. Cloud network logs cannot be erased or cleaned by an attacker and what is reported from the network is undoubtedly what happened.
Finally, there is a new and very important reason to have cloud network telemetry in place: Cost!
- In the days of traditional data centers, you invested into a certain network capacity (10Gbps, 40Gbps, or 100Gbps connectivity) until you reached that limit the marginal cost of any new east-west traffic would be zero.
- In a cloud environment, while you have an (almost) unlimited scalability, every byte you carry comes at a cost. All traffic that is uncontrolled or illegitimate will also be reported on your cloud bill.
This is a major risk in complex and dynamic environments as cost becomes unpredictable. Knowing about cloud traffic flows becomes crucial to:
- Avoid misconfigurations leading to increased cloud bandwidth costs
- Optimize cloud bandwidth costs
- Receive alerts of any changes in behavior or abnormal cloud traffic and anomalies
>> Download Now: Cloud Visibility [Free Whitepaper]
Cloud Traffic Monitoring - Capturing Packets in the Vloud
In order to monitor your network cloud traffic, you need packet capture functionality. With limited access to the network layer and inability to use any form of SPAN, a genuine copy of the production traffic in the cloud is necessary, which is a new challenge compared to an on-premise data center.
Cloud vTAPs are used to send copies of the traffic to a network analyzer to provide critical insight into IT services, applications, and infrastructure performance. The virtual TAP allows you to easily deploy the monitoring application across the whole network, leaving a blueprint for scaling future growth.
Deploying Garland Prisms mirrors 100% of your out-of-band and passive traffic to the Accedian Skylight. This cloud TAP solution captures and organizes cloud packet traffic from cloud provider infrastructures, including Azure and AWS, while processing cloud workloads like VMs and containers. When delivered to the Accedian Skylight, you will receive all “east-west” and “north-south” transaction traffic in the cloud, enabling you to rapidly detect performance degradations, anomalous behavior, and other issues that can negatively impact your cloud applications.
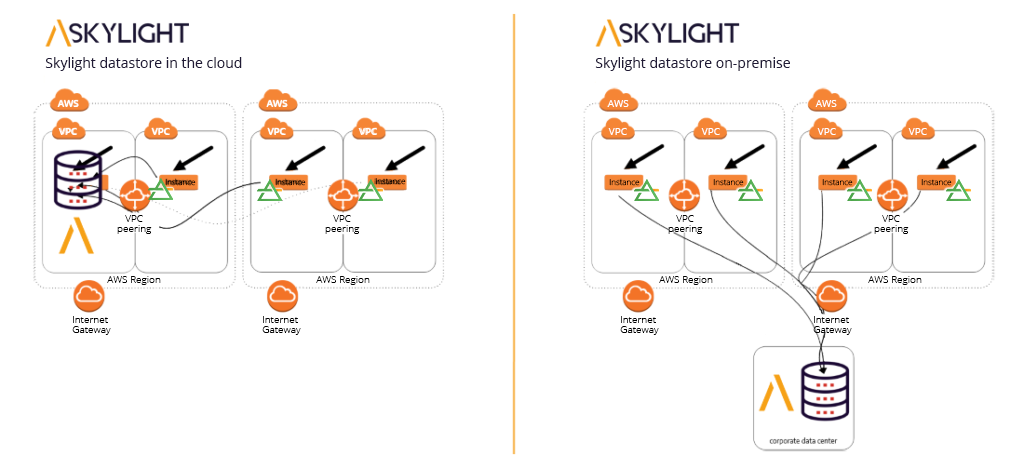
Accedian’s Skylight and Garland Technology solution is not only valuable for existing hybrid solutions, but also for cloud migrations. The combined cloud solution allows you to answer the unknown exchanges of impacted tools and the user experience. During a cloud migration, the Skylight helps to evoke the correct applications, systems, and servers. Whether sitting in a hybrid environment or performing a full cloud migration, the Accedian and Garland cloud solution deployment allows full monitoring for peace of mind.
Looking to add visibility to your cloud deployment, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do!

