

Garland Technology and BluVector® are dedicated to sharing network connectivity best practices and inline security management, propagating why having reliable data in your network is incredibly important for security.
BluVector, recently acquired by Comcast, is a leading network security provider. The data BluVector provides empowers security teams to uncover real threats, allowing business and governments to operate with confidence that their systems are protected.
Garland Technology’s EdgeSafe™ Bypass TAPs provide 100% visibility, and 360° views for BluVector sensors to monitor north-south traffic and the flows getting past firewalls. The sensors can also be deployed on an internal LAN segment to acquire data related to lateral movement of threats in the network. Once the data is collected and put into a collector mode through the device, the traffic can be measured and segmented with machine learning and aggregated event data, which is then forwarded to a SIEM.
As data centers grow, data segment applications and additional data to manage can grow exponentially. It’s the natural evolution of services being provided, which can be challenging to scale, thus introducing bottlenecks and opportunities for downtime. To mitigate this risk, a toolset for performance, monitoring & analytics, or active security is needed for visibility into the network.
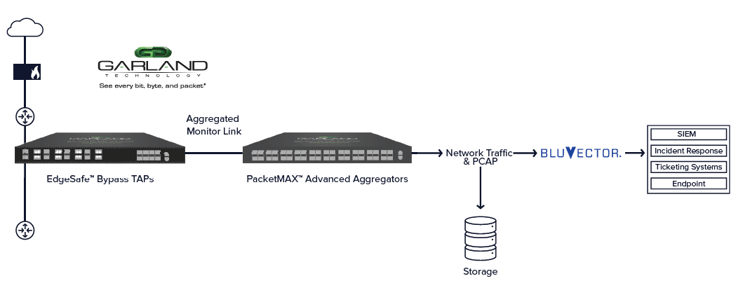
Before passing through the BluVector scalable file analyzer, the reassembled packets carve out metadata and files. The data going into BluVector is primarily live traffic, therefore files or PCAP data can be submitted in parallel. Once the data is passed, a series of different engines analyze the data. The Core engine is the machine learning engine where about 40 different file types are uncovered.
From the data fed from the Network TAPs into BluVector sensors, a speculative code execution engine is used. This coding primarily focuses on two things:
BluVector will carve out JavaScript segments from the wire. Using the speculative coding, the segments are inspected for suspicious intent with 100% code coverage. The platform uses a series of heuristics when the malicious code has been identified.
BluVector shows what has been determined malicious through a list of event cards representing a high level of information. The event detail shows everything captured by the Zeek metadata and from the Garland Network TAP. Since every piece of the data is logged and connected, BluVector filters and indexes the information automatically. This produces a great visual of the time the event took place. As an analyst, this is important to drill into the transferred executable file to see immediately where the metadata and file type is located.
Machine learning is used to train the data as events are adjudicated. The events are marked as malicious or false positive automatically, providing batch training systems and statistically sampled data. In order for BluVector sensors to analyze malicious data, a Bypass TAP is needed to provide live traffic. This starts at the foundational layer providing multi mode tool capabilities and visibility into the environment. Garland Technology's Network TAPs allow the right data to be driven to the right place at the right time.
{Ready to learn more about how BluVector and Garland Technology work together to deliver high-fidelity detection, at scale and in real-time? Watch our latest webinar today!}
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.