

There have been quite a few posts about the benefits of Bypass TAPs and how they can keep the network up and running in the event an inline appliance fails. But what about situations where the inline appliance is the main source of security for the network, and the company has zero tolerance for unsecured traffic? In those cases, the Bypass TAP has a “Reverse Bypass Mode” to accommodate for just that.
With reverse bypass mode, the Bypass TAP still sends out heartbeats to the connected inline appliance. If the inline appliance fails for any reason, the heartbeats will stop and the Bypass TAP will respond by failing closed: turning the network ports off to shut down the flow of traffic. This will prevent unsecured traffic from entering or leaving the network.
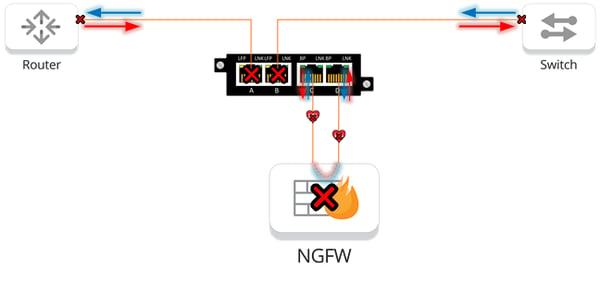
By shutting down the network ports, reverse bypass mode kills the link between the network devices and the TAP. If the network devices have a redundant link or an established HA process, the loss of link from reverse bypass mode will trigger the established failover process.
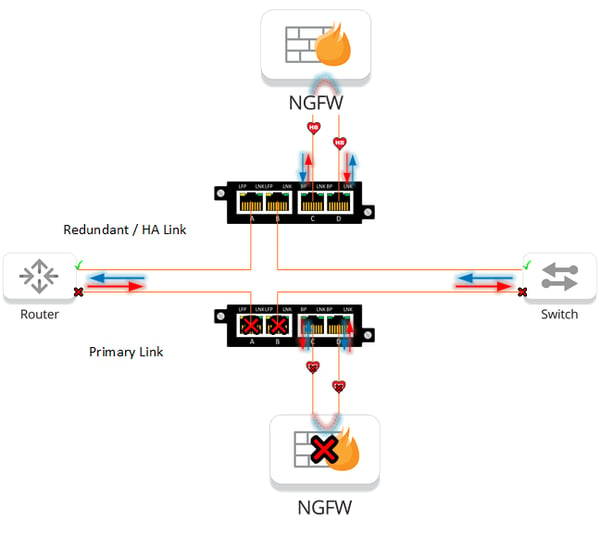
But what’s the point of this? If the failed appliance would take down the network anyway, why bother installing a Bypass TAP in the first place? The answer is the additional quality of life features provided by the Bypass TAP. Bypass TAPs can expedite troubleshooting by using forced bypass mode to rule out devices when experiencing issues. Bypass TAPs with controller cards can also send alerts to administrators when appliances go down, adding greater context to network failures.
Bypass TAPs have the capability to match whatever your network needs, whether they prioritize security or connectivity. Having a Bypass TAP in front of every in-line appliance adds functionality and resiliency to the network without creating any new points of failures.
Looking to add a bypass solution to your security deployment, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do!
If the inline security tool goes off-line, the TAP will bypass the tool and automatically keep the link flowing. The Bypass TAP does this by sending heartbeat packets to the inline security tool. As long as the inline security tool is on-line, the heartbeat packets will be returned to the TAP, and the link traffic will continue to flow through the inline security tool.
If the heartbeat packets are not returned to the TAP (indicating that the inline security tool has gone off-line), the TAP will automatically 'bypass' the inline security tool and keep the link traffic flowing. The TAP also removes the heartbeat packets before sending the network traffic back onto the critical link.
While the TAP is in bypass mode, it continues to send heartbeat packets out to the inline security tool so that once the tool is back on-line, it will begin returning the heartbeat packets back to the TAP indicating that the tool is ready to go back to work. The TAP will then direct the network traffic back through the inline security tool along with the heartbeat packets placing the tool back inline.
Some of you may have noticed a flaw in the logic behind this solution! You say, “What if the TAP should fail because it is also in-line? Then the link will also fail!” The TAP would now be considered a point of failure. That is a good catch – but in our blog on Bypass vs. Failsafe, I explained that if a TAP were to fail or lose power, it must provide failsafe protection to the link it is attached to. So our network TAP will go into Failsafe mode keeping the link flowing.
Single point of failure: a risk to an IT network if one part of the system brings down a larger part of the entire system.
Heartbeat packet: a soft detection technology that monitors the health of inline appliances. Read the heartbeat packet blog here.
Critical link: the connection between two or more network devices or appliances that if the connection fails then the network is disrupted.