As the modern cybersecurity stack grows with an array of threat detection and response tools critical to protecting IT data, active blocking tools like Intrusion prevention systems (IPS), Web Application Firewalls (WAF), and next generation firewalls (NGFW) are still the backbone of network cybersecurity.
According to a recent Imperva report, “The number of compromised records year-over-year has grown, on average, an astounding 224 percent since 2017,” and predicts that 2021 will see around 1,500 data breach incidents with a total of 40 billion compromised records, and an average of 26 million compromised records per breach.
The goal of real-time prevention is to set your organization up to better defend against this rise in breaches, compromises, and business risks. As teams expand their security position from detection-only to proactive prevention and response, a top-down approach factor in tool availability and redundancy to ensure optimal network protection from downtime and accurate visibility.
Why Use A Bypass TAP?
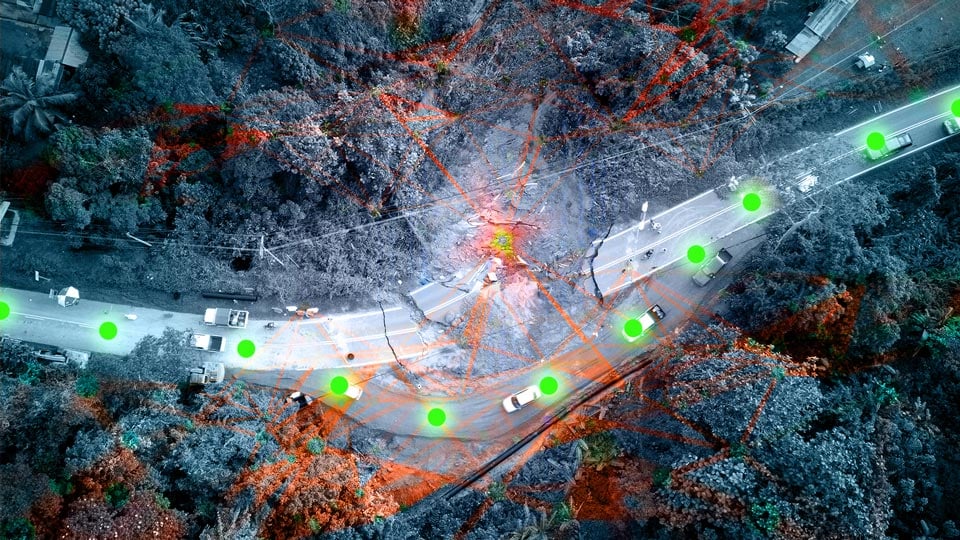
Tools like WAF, IPS, and firewalls sit inline, meaning they are actively blocking threats as traffic passes through critical links on the network. As important as they are to cybersecurity tools, architecting and managing deployments, updates and failures become just as important for network and business availability. Because they sit in the stream of traffic, deployment, management, and replacement of these devices must be planned out in advance.
That is why inline security tools rely on external bypass TAPs. The Bypass TAP (also referred to as a bypass switch) was developed specifically to resolve the issue of these inline tools causing a single point of failure (SPOF) in the network – leading to network downtime and a possible security lapse. In the event an inline device becomes unavailable, it is bypassed and traffic is automatically forwarded around the failed tool.

As you can see in this diagram, the Bypass TAP is the connectivity between the network and the inline tool (Edge Firewall), passing traffic to be inspected. Heartbeat packets monitor the health of the inline device, instantly bypassing the device during a failure, keeping the network up.
Is it Better to Use An Internal vs External Bypass?
So why not use the internal bypass feature in the inline tools? I hear this question often speaking to solution architects. And quite simply the question comes down to:
- How critical is the network link? In an unplanned failure of the inline tool, are you ok with the downtime? Can you take the tool offline and physically remove it? This could include cable cuts, transceiver malfunction, inline tool breakdown, and loss of power.
- What is your strategy to deploy or replace? Wouldn’t it speed up deployment and troubleshooting to be able to have access to the link, and all you need to do is connect and disconnect the tool without affecting the live network?
- Does the tool have proper bypass capabilities? Many have them only available for specific speeds, mainly 1G. External bypass TAPs are available from 1G to 100G.
- What is your IPS or WAF designed to do? A bypass TAP is a simpler device than the security tool, and is designed for fault tolerance. It is purpose-built to monitor and manage the availability of the tool. That is its core function.
- What is the cost? – Bypass features for an inline tool can come as license fees, which over time TCO (Total cost of ownership) can run more than the external Bypass TAP.
The Goal Is to Ensure Continued Availability
As cybersecurity strategies deploy active blocking tools to protect against incoming threats and breaches, ensuring these tools have continued availability and reliability is the next step.
An external Bypass shouldn't be seen as a negative towards the inline tool, but an enhancement – to allow the tool to focus their processing power on securing the network. Where the external bypass' sole focus is to make sure the tools is working 24/7/365.
Utilizing an external Bypass TAP, and not relying on bypass functionality within your inline tool, offers the unique ability to implement inline lifecycle management. From sandboxing a new tool deployment to easily taking tools out-of-band for updates, installing patches, performing maintenance or troubleshooting to optimize and validate before pushing back inline, a Bypass TAP has quickly become the essential complement to any inline tool.
Garland Technology’s industry-leading bypass product line has a solution for any environment. EdgeSafeTM Bypass TAPs from 1G to 100G and the innovative EdgeLens® hybrid inline packet brokers combine the resiliency and reliability of a bypass tap with the functionality of a packet broker with advanced filtering, out-of-band tools and provide High Availability [HA] architecture from one device. All designed to simplify the modern security stack.
Looking to add an external bypass solution to your inline security tool deployment, but not sure where to start? Join us for a brief network Design-IT consultation or demo. No obligation - it’s what we love to do.