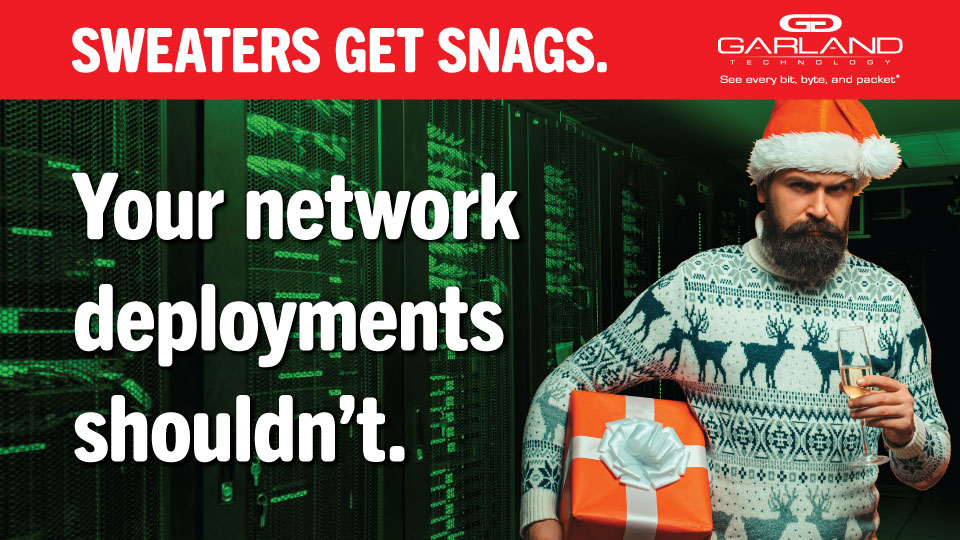
Don’t let snags unravel IT network deployments
Maximizing the merriment in December requires Santa-like scheduling superpowers. There are friends and family to visit, gifts to buy, cookies to bake, and Hallmark movies to binge. Likely, there’s...